May 12, 2026
Microsoft Enterprise License: SMB Guide 2026Navigate Microsoft Enterprise License. Our Canadian SMB guide compares M365 E3/E5, costs, models, & compliance to help you choose the right plan.
Read Full Post%20(1).webp)
Usman Malik
Chief Executive Officer
March 28, 2026
IT security services are a set of proactive measures and outsourced expertise designed to protect your company’s digital assets. Think of them as a specialized security force for your business, defending you against ever-present cyber threats like data breaches, malware, and ransomware.
Imagine your business as a physical storefront. You would not leave the doors unlocked overnight or ignore a faulty alarm system. The same logic applies to your digital operations, where the threats are often invisible but far more organized.
This is not about scare tactics; it is about understanding the reality Canadian businesses face today. When you demystify IT security services, they stop being a confusing technical cost and become a strategic asset that fuels your growth and protects your bottom line.
Taking a proactive stance on security is simply good business. The alternative is reacting to a crisis after the damage is done—a position that is always more expensive and disruptive. This guide will help you understand the core services that protect you, turning cybersecurity from a defensive headache into a genuine competitive advantage.
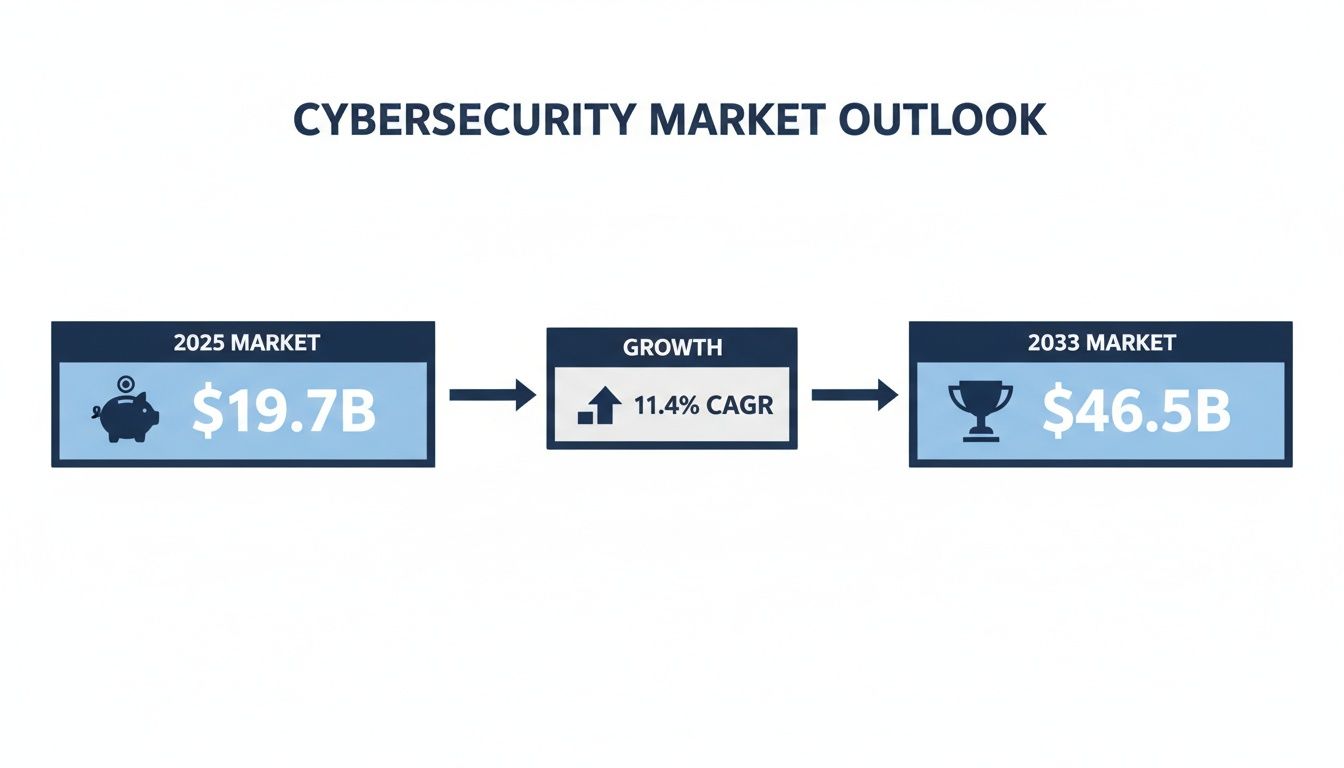
The push for better security is not just a trend; the numbers paint a stark picture. Canada's cybersecurity market is on a steep climb, projected to grow from USD 19.7 billion in 2025 to an incredible USD 46.5 billion by 2033. That is an annual growth rate of 11.4%.
This explosive growth is happening for a reason. It reflects the escalating threats and our increasing reliance on digital systems, especially in critical sectors like healthcare and finance where a single data breach can be crippling.
This financial data tells a clear story:
For business and IT leaders in medium-sized organizations, this is not just an IT issue—it is a fundamental business risk. Ignoring it is like leaving the front door of your office unlocked overnight. You may also want to read about the top cybersecurity threats for SMBs to understand the risks better.
Think of your business's digital security like a medieval fortress. A single wall will not suffice. To truly defend against modern threats, you need multiple, overlapping layers of defence. Simply relying on one tool, like antivirus software, is like having a strong front gate but leaving the rest of the walls completely unguarded.
A proper security strategy combines specialized IT security services, with each one designed to stop a specific type of attack. It might sound complex, but the idea is simple. Each service acts as a different part of your defence system, and when they work together, they create a powerful barrier that keeps attackers out.
The demand for these protective services is growing fast as more businesses awaken to the risks. The numbers speak for themselves, showing a massive increase in spending on cybersecurity in Canada.
This growth sends a clear message to business leaders: investing in strong IT security services is no longer an optional expense. It is a fundamental cost of doing business safely and securely.
To help you understand how these services protect your business, we have broken down the core components. This table shows what each service does and, more importantly, the business problem it solves.
| Security Service | Primary Function | Key Business Benefit |
|---|---|---|
| Threat Detection & Response | Actively hunts for and neutralizes cyber threats in real-time, 24/7. | Prevents breaches by stopping attacks before they can cause damage. |
| Endpoint Protection | Secures all devices (laptops, servers, phones) from malware and unauthorized access. | Protects your entire network from being compromised by a single infected device. |
| Vulnerability Assessments | Proactively scans systems for security weaknesses and missing patches. | Seals security gaps before attackers can find and exploit them. |
| Managed Firewall | Manages and updates your network's main gatekeeper to block malicious traffic. | Ensures your first line of defence is always strong and up-to-date. |
| Email Security | Filters incoming emails to block phishing, malware, and spam. | Protects against human error by stopping threats from reaching employee inboxes. |
Each of these services plays a vital role. Let us dig a little deeper into how they work together to create that layered defence your business needs.
Imagine having guards patrolling your fortress walls 24/7, actively looking for any sign of trouble. That is Threat Detection and Response. This service is not about passively waiting for an alarm to go off; it involves actively hunting for suspicious activity that could be the start of an attack.
Security experts use sophisticated tools to monitor your network around the clock. If they spot an anomaly—like an employee’s account trying to access highly sensitive files at 3 a.m.—they act on it immediately. This proactive stance means most threats are neutralized long before they can do any real harm.
Every device connected to your network is an "endpoint." This includes everything from laptops and servers to mobile phones. Think of each one as a potential gate into your digital fortress. Endpoint Protection places a dedicated sentry at every single one of those gates.
Modern endpoint protection goes far beyond traditional antivirus. It uses advanced methods to block malware, stop unauthorized access, and even isolate a device if it becomes compromised. This is crucial because it stops an infection on one person's laptop from spreading across your entire company. To get a better understanding of this, you can learn more about what endpoint detection and response is in our detailed guide.
A strong defence requires protecting every potential point of entry. A single unprotected laptop used by a remote employee can become the weak link that brings down your entire network.
Even the strongest fortress can develop cracks and weaknesses over time. A Vulnerability Assessment is like hiring a structural engineer to methodically inspect your walls, towers, and gates for any weak spots before an attacker does.
This service involves regularly scanning your systems, software, and network for known security holes. For instance, a scan might reveal that a critical server is missing a recent security patch, leaving it exposed. By finding and fixing these vulnerabilities proactively, you are essentially sealing the cracks in your defences before they can be exploited.
Your network's firewall is the main gatekeeper to your fortress. It is responsible for inspecting all traffic coming in and going out. A Managed Firewall service ensures this gatekeeper is always alert, correctly configured, and updated to recognize the very latest threats.
Without expert management, a firewall’s rules can become outdated and ineffective. Cybercriminals are constantly finding new ways to sneak past weak or poorly configured defences. A managed service provider ensures your firewall rules are always optimized to block malicious traffic while letting legitimate business activities run smoothly.
Email remains one of the most common ways attackers breach an organization's defences. They often use phishing—deceptively crafted messages designed to trick your staff into giving up passwords or downloading malware. Email Security services act as a strict inspection point for every single message that comes through.
These systems use advanced filters to analyze incoming emails for any sign of malicious intent. They can automatically quarantine suspicious messages, strip out dangerous attachments, and flag potential phishing attempts for your users. This adds a critical layer of protection against human error, which is often the weakest link in any security chain.
While fundamental defences like firewalls and endpoint protection are your digital fortress's essential walls, they are mostly reactive. To truly get ahead of today’s cyber attackers, you need to shift from a defensive crouch to a forward-leaning, proactive stance. This means actively hunting for threats, not just waiting for an alarm to go off.
That is exactly what advanced IT security services are built for. They take you beyond simple prevention and into active surveillance, strict access controls, and solid recovery plans. These strategies build real operational resilience, ensuring your business can not only survive an attack but continue to operate securely.
The market shows a clear trend toward this proactive approach. Canada's Security Services industry is expected to reach a market size of $8.3 billion by 2026. A huge part of that is Security-as-a-Service (SECaaS), which is forecast to jump from USD 914.24 million in 2025 to over USD 3.7 billion by 2035. With North America making up nearly 40% of the global managed security market, the demand for advanced solutions is undeniable. You can see more data on Canada's security services industry on ibisworld.com.
Think of Managed Detection and Response (MDR) as having an elite special forces team protecting your digital assets. This service is not about just monitoring alerts; it is a dedicated team of security experts actively hunting for threats inside your network, 24/7.
MDR brings together sophisticated technology and sharp human intelligence to spot the subtle signs of a compromise that automated tools often miss. When they find a potential threat, the MDR team does not just send an alert and walk away—they investigate it, contain the threat, and remove the attacker.
For a medium-sized business, MDR delivers enterprise-grade threat hunting without the staggering cost and complexity of building an in-house Security Operations Centre (SOC). It is about having true experts in your corner, ready to act instantly.
This proactive method is essential for stopping sophisticated attacks, especially those that use stealthy tactics to hide for weeks or even months. By finding and stopping intruders early, MDR prevents a minor security incident from becoming a devastating data breach. To see how this fits into a wider strategy, check out our guide on choosing the right MSSP security services.
If your network is a fortress, then Identity and Access Management (IAM) is the advanced access control system that guards every single door. It is a framework of policies and technologies designed to ensure the right people get access to the right resources, at the right times, and for the right reasons—and nothing more.
IAM is much more than just a username and password. It involves critical components like:
In our current world of remote work and cloud applications, managing who has access to what has become more critical than ever. A solid IAM strategy is your best defence against unauthorized access, whether it is an external hacker with stolen credentials or an internal threat. A proactive defence must also account for risks from within, as detailed in this a practical guide to detecting and preventing insider threats.
Let us be realistic: no defence is 100% foolproof. That is why the final piece of any proactive security strategy must be a robust "what if" plan. Backup and Disaster Recovery (BDR) is your ultimate safety net, ensuring you can restore your operations quickly and completely after a major incident.
This goes far beyond just copying files to an external drive. A modern BDR solution includes:
Whether you are hit with a ransomware attack, a critical hardware failure, or a natural disaster, a strong BDR plan means you are not starting from zero. You are just executing a well-rehearsed plan to get back to business, protecting your revenue, reputation, and the trust you have built with your customers.
For any Canadian business, strong cybersecurity is not just about warding off attacks; it is about following the law. Failing to protect sensitive information can do more than just tarnish your reputation—it can land you in serious legal and financial trouble.
The key is to view compliance not as a roadblock, but as a blueprint for building trust and a more resilient business.
This means understanding the specific regulations that apply to you and weaving the right security controls into your everyday work. For a growing business, that responsibility can feel overwhelming, but it does not have to be. With the right IT security services, meeting these legal standards becomes a manageable, integrated part of your security strategy.
Let us cut through the legal jargon and look at what these rules really mean for your business—and how a good partner can help you achieve compliance.
At a national level, PIPEDA is the rulebook for how private-sector companies in Canada collect, use, and share personal information. It demands that you are open about how you handle customer data and that you protect it with appropriate safeguards.
Imagine a law firm in Vancouver with sensitive client files. Protecting that data goes way beyond just setting passwords. It means putting specific, expert-level controls in place, which is exactly where IT security services come in. This includes things like:
Failing to comply with PIPEDA can lead to massive fines—up to $100,000 for every single violation. Even worse, a breach of trust can do permanent harm to your client relationships. You can dive deeper into this topic in our guide on effective data security management.
If PIPEDA sets the rules, a SOC 2 report is how you prove you are actually following them. This is especially true if you handle data for other businesses. Think of it as an independent audit that verifies your security is up to standard, showing clients and partners that you are a safe pair of hands for their information.
A SOC 2 audit measures your systems against five "Trust Services Criteria":
For a growing Canadian tech company offering a software-as-a-service (SaaS) platform, achieving SOC 2 compliance is not just a security exercise—it is a huge business advantage. It sends a powerful signal to potential enterprise customers that you take security seriously.
For businesses in certain industries, the rules get even tighter. In healthcare, provincial laws like Saskatchewan's Health Information Protection Act (HIPA) or Ontario's Personal Health Information Protection Act (PHIPA) set incredibly strict standards for protecting patient records.
These regulations are not just suggestions; they are legal requirements with steep penalties for non-compliance. Working with an IT security services provider who understands your specific industry is essential for navigating these complex rules and implementing the necessary technical safeguards to protect your business.

Choosing a managed security service provider (MSSP) is a high-stakes decision. Think of it like hiring the master architect to build your company’s digital fortress. The right partner becomes a genuine asset, a silent force empowering your growth and resilience.
But the wrong one? That can leave you with a false sense of security, which is often more dangerous than having no protection at all.
Making the right choice means looking past a simple list of services and prices. You need a partner who understands your business, your industry, and the Canadian regulatory landscape inside and out. It is about finding a proactive team that stops problems before they start, not a reactive vendor who only appears after things have gone wrong.
The demand for these services is skyrocketing. Canada's security market reached USD 6,604.6 million in 2024, and it is the 'service' segment that is growing fastest as cyber risks mount. While hardware and software used to consume security budgets, it is the expert it security services that will truly protect your business from modern threats.
Here is the thing: not all MSSPs are created equal. A provider that mainly works with retail clients will have a completely different skillset than one that understands the rigid compliance needs of a healthcare clinic or a law firm.
Look for a partner with proven, demonstrable experience in your specific field. They should speak your language, understanding the daily operational challenges and regulatory pressures you face. Ask for case studies or even references from businesses like yours. It is the single best way to confirm they have the real-world experience to protect your organization effectively.
A partner with that deep industry knowledge does not just secure your data—they can help you use technology to get a leg up on the competition. Because they understand your workflows, they can implement security solutions with minimal disruption to your operations.
For any Canadian business, data sovereignty is a massive issue. Where your data is stored and who has access to it matters—for compliance, and for your own peace of mind. Partnering with a provider whose entire team and infrastructure are based in Canada gives you some critical advantages:
When your security team is 100% Canadian, you eliminate the complexities and risks of international data handling. It is a straightforward way to keep your data safe and compliant, right here at home.
For many organizations in healthcare, finance, and the public sector, this is non-negotiable. To help make an informed choice, a practical guide to managed network security solutions can be an invaluable resource.
Once you have a shortlist of potential partners, it is time to dig in. The answers to these questions will tell you a lot about their processes, their expertise, and how much they actually care about their clients.
A potential partner should welcome these questions and give clear, confident answers. If you get vague responses, that is a major red flag. For a more detailed look at this process, our article on how to pick a cyber security service partner can help you prepare.
Finding the right it security services provider is about building a long-term, trusted relationship.
We have covered a lot of ground together, from laying the first bricks of your digital defences to choosing the right partner to manage them. If there is one thing to take away from this guide, it is this: comprehensive, proactive IT security services are not a luxury reserved for large corporations. They are an absolutely essential investment for any Canadian SMB serious about protecting its assets and earning client trust.
You now have the knowledge to move from a place of uncertainty to one of confident, clear-headed action. What once might have seemed like abstract jargon—from threat detection to compliance—should now feel like tangible, critical business functions. You can see how these services weave together to form a resilient shield around your operations, your data, and your hard-won reputation.
The logical next step is putting that knowledge to work. Reading and understanding is half the battle; applying that understanding is what truly secures your business's future.
You do not have to take this next step alone. The path to a stronger security posture begins with a single, simple action: understanding where you currently stand. A thorough assessment is the starting point for any meaningful improvement in your defences.
To move forward, you need a clear, objective view of where you are right now. This means identifying existing vulnerabilities, recognizing any compliance gaps, and understanding which risks pose the greatest threat to your specific business. This process is the foundation of your strategic roadmap.
We invite you to schedule a no-obligation security assessment with our 100% Canadian-based team. Think of it less as a sales call and more as a collaborative working session designed to give you immediate value. Our experts will help you:
Take that first step today. Let us help you transform security from a source of anxiety into a genuine competitive advantage.
Even after seeing the clear benefits, it is natural for business leaders to have some practical questions before committing to IT security services. Here are some of the most common ones we hear from medium-sized businesses across Canada, along with some straightforward answers.
The cost of professional IT security services depends on your company’s size, the complexity of your IT environment, and exactly which services you need. Most managed security providers will offer a few pricing tiers or work with you to build a custom package.
For a mid-sized Canadian business, this can range from a few hundred to several thousand dollars per month. It is important to see this as an investment in protecting your business, not just another line item on the expense sheet. The cost of a single successful data breach—in downtime, fines, and lost trust—is almost always far higher. A good partner will always start with an assessment to give you a transparent quote that fits your specific needs and budget.
It is very common for businesses to rely on a small IT team or even a single "do-it-all" IT generalist. They handle everything from helpdesk tickets to bigger projects, and they are invaluable. However, cybersecurity is its own highly specialized field, one that changes at a breakneck pace. It is simply not realistic to expect an in-house generalist to have the same capabilities as an entire team of dedicated security experts.
A managed security service is designed to complement, not replace, your existing IT resources. It gives you access to a team of dedicated specialists, advanced security tools, and 24/7 monitoring that would be incredibly expensive to build on your own. This frees up your internal team to focus on projects that drive the business forward, creating a 'co-managed' partnership that gives you the best of both worlds.
The timeline for getting set up depends entirely on the services being rolled out. Any reputable partner will walk you through a structured and transparent onboarding process, making sure the transition is smooth and causes minimal disruption to your daily work.
Right from the start, a trustworthy provider will give you a clear project plan with defined milestones and realistic timelines. You will never be left in the dark, and you will know exactly what to expect at every step.
Take the first step toward a more secure future for your business. The expert team at CloudOrbis Inc. offers a no-obligation security assessment to help you identify vulnerabilities and build a clear, actionable roadmap. Book your assessment with our 100% Canadian-based team today.
May 12, 2026
Microsoft Enterprise License: SMB Guide 2026Navigate Microsoft Enterprise License. Our Canadian SMB guide compares M365 E3/E5, costs, models, & compliance to help you choose the right plan.
Read Full Post
May 11, 2026
How to Protect Your Database: A Guide for Canadian SMBsLearn how to protect your database with our step-by-step guide for Canadian SMBs. Covers encryption, access controls, backups, and HIPAA/PIPEDA compliance.
Read Full Post
May 10, 2026
Best Data Centers In Calgary 2026: SMB GuideExplore our 2026 guide to the top data centers in Calgary. We compare 7 key players on uptime, security, and connectivity for SMBs.
Read Full Post