
June 10, 2026
Unlock Insights: Analytics and Reporting for SMBs 2026Unlock growth with strategic analytics and reporting. Our guide helps Canadian SMBs turn data into actionable insights for compliance & ROI.
Read Full Post%20(1).webp)
Usman Malik
Chief Executive Officer
March 12, 2026
Endpoint Detection and Response (EDR) is a powerful cybersecurity tool that gives businesses real-time monitoring and response capabilities to shut down active threats. Unlike standard antivirus software that mainly blocks known threats, EDR is designed to actively hunt for, investigate, and stop sophisticated attacks on devices like laptops, servers, and mobile phones.
Think of your business as a high-security building. Every laptop, server, and company phone—your endpoints—are the doors and windows. Traditional antivirus software is like a basic lock on each one. It's great at keeping out known criminals whose faces are on a wanted poster. But what happens when a skilled intruder picks the lock or finds an open window?
This is where it pays to understand what is endpoint detection and response. Picture EDR as a highly-trained security guard stationed at every single entry point. This guard isn't just checking IDs against a list; they are constantly watching for any suspicious behaviour.
EDR technology works on the assumption that a breach isn't a matter of if, but when. Its whole purpose is to give you the visibility and tools to find and stop attackers before they can do real damage, which is a big change from a purely preventative security model.
EDR goes far beyond what a simple lock can do. It tracks an attacker's every move, analyzes their actions to spot unusual patterns, and takes immediate steps to contain the threat. This is non-negotiable for Canadian businesses, particularly in regulated industries like healthcare or finance where data is everything.
For these organizations, just locking the doors isn't enough anymore. You need active surveillance to defend against modern cyber threats. Understanding how EDR fits into a broader strategy for data security is key to building a truly strong defence.
As a result, EDR adoption is skyrocketing. In Canada, the market is projected to hit an estimated $6.8 billion by 2031. This trend is especially relevant for small and mid-sized businesses in hubs like Toronto, Calgary, and Edmonton, as cyberattacks targeting Canada's digital backbone become more advanced. You can see the full report on Canada's EDR market growth. This growth really drives home the need for a modern way to secure your business assets. To get a better handle on the fundamentals, you can read our guide on what is cybersecurity.
To really understand what endpoint detection and response brings to the table, it helps to look under the hood. Unlike old-school antivirus that just checks files against a list of known threats, EDR works more like a sophisticated surveillance system for your entire network, constantly watching and analyzing activity.
It’s a powerful, ongoing cycle built on three core pillars: gathering comprehensive data, using that data for intelligent threat detection, and enabling a swift, decisive response.
This visual breaks down the shift from the traditional antivirus model to the modern EDR approach, showing how EDR adds a much more active and intelligent layer of security.
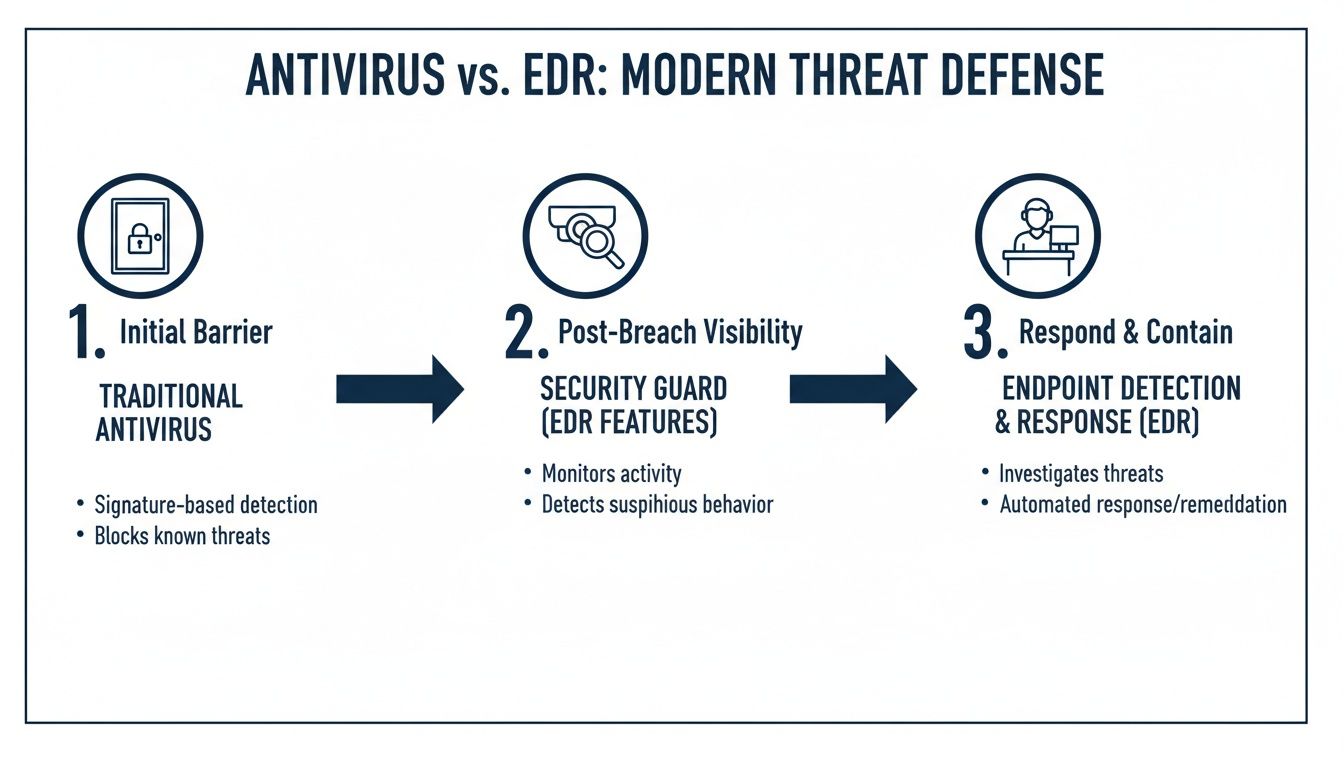
The real takeaway here is the move from a passive, gate-based defence to an active, intelligence-driven one. Think of it as upgrading from a simple lock on the door to a dedicated security guard who actively patrols the premises.
It all starts with a lightweight software agent installed on every endpoint—your laptops, desktops, servers, and even mobile devices. Think of this agent as a flight data recorder for your IT environment. It meticulously and continuously records a huge range of telemetry data, all in real-time.
And this isn't just about scanning files. The agent captures incredibly granular details about everything happening on the device:
This rich stream of data is funnelled from all your endpoints to a central hub, usually a cloud-based platform. This creates a complete, searchable history of all activity across your network, which becomes the foundation for everything that comes next. Effective data gathering is vital, and you can learn more about how to stay ahead of cyber threats with event logging in our detailed guide.
Once all that data is centralized, the real analysis begins. This is where an EDR solution truly separates itself from older technologies. Instead of just looking for known malware signatures, modern EDR platforms use multiple advanced techniques to spot threats that would otherwise fly completely under the radar.
This detection phase is a combination of several powerful methods:
When a potential threat is identified, the EDR system generates a high-fidelity alert. It correlates all the related events into a single, clear story of the attack—how it started, what it did, and where it tried to go. This context is absolutely critical for a fast and effective response.
Spotting a threat is only half the battle. The final and most critical step is doing something about it. EDR gives security teams both automated and manual tools to contain threats and fix the damage—fast. These response actions can stop an attack in its tracks, often within seconds of being detected.
Key response capabilities include:
This powerful combination of deep visibility and rapid response capabilities is what makes endpoint detection and response an essential defence for any modern business. It gives you the power not just to see attacks, but to stop them before they turn into a devastating data breach or ransomware incident.
What really separates a powerful Endpoint Detection and Response (EDR) solution from a basic security tool? It all boils down to four critical capabilities. For business and IT leaders, understanding these features makes it clear how EDR shifts your cybersecurity from a passive, reactive stance into an active, intelligent hunt for threats.
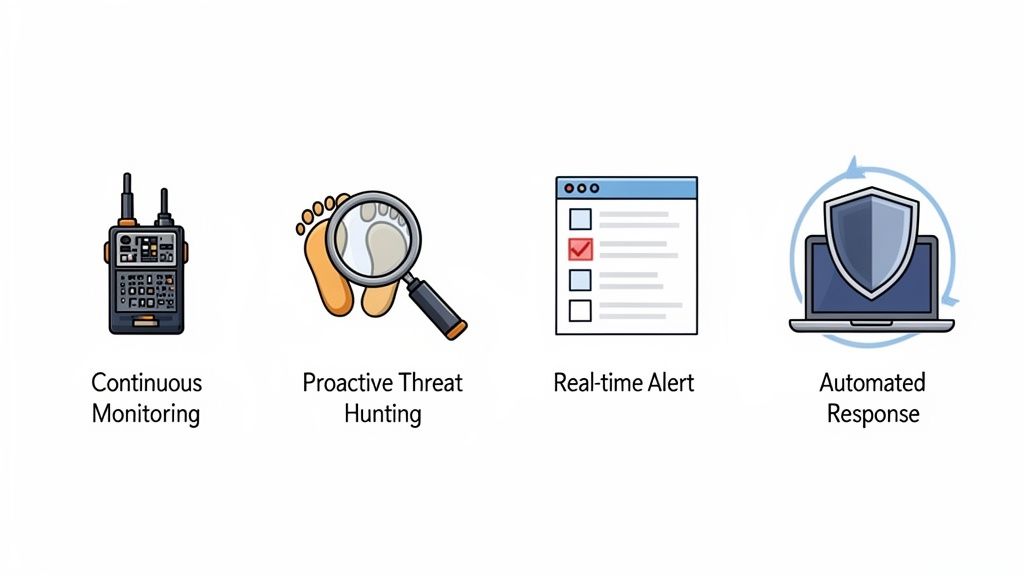
These capabilities don’t work in isolation; they create a unified security framework that provides both depth and breadth. Together, they deliver the visibility, analytical power, and response tools needed to stop modern attacks in their tracks.
To help translate these technical functions into clear business outcomes, here’s a quick breakdown of how each core EDR capability directly impacts your organization's security and operational health.
Each of these pillars is essential for building a resilient cybersecurity posture. They work in concert to ensure that threats are not only detected but also thoroughly understood and neutralized before they can cause significant harm.
At its heart, a modern EDR platform provides continuous monitoring and recording of everything happening on your endpoints. Think of it as a flight data recorder for every laptop, server, and mobile device in your company. This function captures a detailed, searchable log of every process that runs, every file that’s changed, and every network connection that’s made.
This complete visibility isn't a luxury anymore; it's a must-have for effective incident investigation and compliance. When a security issue pops up, your team can hit rewind and see exactly how an attacker got in, what they did, and which systems were touched. This forensic trail is priceless for ensuring a complete cleanup.
Without this deep visibility, security teams are essentially flying blind. They might see an alert, but they have no context to understand where it came from or what its impact is, making a proper response nearly impossible.
While automated detection is powerful, some of the most skilled adversaries know how to stay hidden. This is where proactive threat hunting becomes a game-changer. EDR platforms give security experts the tools they need to actively search for signs of a compromise that automated systems might otherwise miss.
Threat hunters use the rich data collected by the EDR to form hypotheses about potential threats. For example, a hunter might look for a legitimate system tool, like PowerShell, being used in an unusual way—a common tactic for attackers trying to blend in with normal activity. This human-led investigation adds a vital layer of defence.
We've seen recent malware campaigns use legitimate cloud services and scripts to evade traditional security tools. Proactive hunting allows analysts to spot these subtle behavioural red flags before they escalate into a full-blown incident.
One of the biggest struggles in security operations is "alert fatigue"—the constant, overwhelming flood of notifications from different tools. A strong EDR solution tackles this head-on with real-time alerting and intelligent triage. It uses AI and machine learning to analyze events, connect related activities, and filter out the noise.
What this means for your team is that they only get high-quality alerts for threats that actually matter. Instead of sifting through thousands of low-level notifications, they receive a prioritized list of incidents that tells a clear story of the attack.
This capability ensures that your team's limited time is spent investigating and responding to real threats, not chasing down false alarms. It turns a chaotic stream of data into focused, actionable intelligence.
When a credible threat is found, speed is everything. Automated response and remediation features allow an EDR solution to act in milliseconds to contain an attack. This automation drastically shrinks the window for potential damage and business downtime.
Common automated responses include:
These automated actions serve as the first line of defence, containing the immediate threat while security analysts dig deeper. When an incident escalates, having a clear plan is crucial. Knowing what to do after a data breach is a key part of any modern security strategy, and this automation is the first and most critical step in that process.
The world of cybersecurity is swimming in acronyms, making it tough for business leaders to compare solutions. As you explore what endpoint detection and response is, you're bound to stumble upon a few other common terms. Let's cut through the jargon and clarify exactly where EDR fits in.
Think of your cybersecurity strategy like the layers of security you'd use to protect a valuable asset. Each of these technologies plays a unique role, and understanding the difference is the first step to making a smart investment in your company's protection.
Traditional Antivirus (AV) is the most basic form of endpoint security, and it's probably the one you're most familiar with. It works like a simple lock on your door, built to stop known criminals. AV software relies on a database of "signatures"—digital fingerprints of known malware—and scans files to see if there's a match.
If a file matches a known threat, it gets blocked or quarantined. Simple enough. But its biggest weakness is that it can only stop threats it already knows about. It’s a passive, purely preventative tool that modern attackers can easily sidestep with new malware, fileless attacks, or more sophisticated techniques.
Endpoint Protection Platforms (EPP) are the logical next step up from traditional AV. If AV is a single lock, think of an EPP as a more advanced security system for all your doors and windows. It bundles signature-based AV with other preventative controls to build a much stronger frontline defence.
These extra controls often include:
While EPP is a huge improvement, its focus is still almost entirely on prevention. It’s excellent at stopping threats before they execute, but it has very little to offer when it comes to detecting or responding to an attacker who manages to slip past those initial defences.
This is where Endpoint Detection and Response (EDR) completely changes the game. If AV and EPP are the locks on your building, EDR is the active security guard patrolling the property 24/7. EDR is built on a simple, powerful assumption: eventually, prevention will fail and an intruder will get inside.
Its job isn't just to block threats—it's to detect, investigate, and respond to them in real time. EDR provides the deep visibility needed to see an attack as it's happening and gives security teams the tools to shut it down. As the market for EDR continues to grow, it is fast becoming a non-negotiable part of modern security.
The chart below shows just how rapidly the global EDR market is expected to grow, reinforcing its importance.
This projection highlights a clear trend: businesses are moving beyond simple prevention and investing in the active detection and response capabilities needed to fight modern threats.
Extended Detection and Response (XDR) takes the principles of EDR and applies them across your entire organization. If EDR is a guard focused on your endpoints (laptops, servers), XDR is a centralized security team monitoring your entire IT environment.
XDR platforms collect and analyze data not just from endpoints, but also from:
By connecting the dots between all these different data sources, XDR provides a single, unified view of an attack that might be happening across multiple parts of your infrastructure. This gives you much richer context and allows for more comprehensive, automated responses across your whole technology stack.
Finally, there's Managed Detection and Response (MDR). This isn't a technology, but a service. Think of MDR as hiring an elite security firm to manage all of this for you. An MDR provider, like CloudOrbis, takes powerful tools like EDR or XDR and runs them on your behalf.
With MDR, you get a 24/7 team of security experts who handle the threat hunting, alert analysis, and incident response. This is often the most practical and cost-effective approach for mid-sized organizations that lack the in-house cybersecurity staff to manage a complex EDR tool effectively.
This service model turns a powerful but complex tool into a fully managed security outcome. To learn more about how this works, check out our guide on the benefits of managed detection and response services.
Bringing a new security tool into your business isn’t just about buying software; it’s a strategic decision that changes how you manage risk. For many medium-sized businesses in Canada, a cloud-based Endpoint Detection and Response (EDR) solution is the most practical way forward, offering great scalability without the hefty upfront costs of an on-premise setup.
This cloud model is quickly becoming the norm. In fact, Canadian market forecasts point to a major rise in cloud EDR use, especially for small and mid-sized companies in healthcare, logistics, and construction. The EDR market is projected to grow at a compound annual rate of 24.80% from 2026 onward, a trend that highlights just how much demand there is for effective, scalable security. You can dig deeper into what this means for the Canadian EDR market on Data Insights Market.
But here’s the reality check every business leader needs: EDR is not a 'set-it-and-forget-it' tool. It’s a powerful instrument that demands real skill and attention to work correctly.
An EDR solution generates a constant flow of data and alerts about everything happening on your network endpoints. While this total visibility is its biggest strength, it can also become a massive operational burden for an internal IT team that’s already stretched thin.
Without a dedicated security focus, your team can quickly fall victim to alert fatigue. This is what happens when the sheer volume of notifications makes it impossible to tell a real threat from a false alarm. When that occurs, critical alerts get buried, and the EDR tool you invested in loses its value.
It's like buying a high-performance race car but not having a trained driver or pit crew. The potential is immense, but without the expertise to operate it, you won't win any races—and you might even crash.
This brings us to the second major hurdle: the cybersecurity skills gap. Finding, hiring, and keeping professionals with the specific expertise needed to run an EDR platform is both difficult and expensive. These experts need to be able to:
For most Canadian businesses, building an in-house Security Operations Centre (SOC) with 24/7 coverage simply isn't realistic. This is exactly where many companies stumble—they invest in a powerful EDR tool but don’t have the expert resources to make it work. The operational weight becomes too much, leaving them exposed despite their investment.
This operational reality is why a growing number of businesses are turning to managed security providers. Partnering with a team of experts lets you get the full benefit of enterprise-grade security without the immense in-house headache. To get a better handle on your current security posture, a thorough evaluation is a great place to start; our guide on conducting computer security audits can help you prepare.
So, you understand what Endpoint Detection and Response can do for your business. Now comes the big question: Do you build an in-house security team to run it, or do you partner with a Managed Security Service Provider (MSSP)? This decision will shape your budget, your team’s focus, and how well your organization can stand up to cyber threats.

Going the in-house route gives you direct, hands-on control over your security. You call the shots, manage the tools, and own every step of the response process. But this path comes with some serious costs and complexities that go way beyond just the price of the EDR software.
Building a team from the ground up requires a massive investment in a few key areas:
Beyond the payroll, the biggest hurdle is providing genuine 24/7/365 coverage. Cyberattacks don’t work 9-to-5, and a threat that slips through overnight can become a full-blown disaster by morning. For most mid-sized businesses, staffing a round-the-clock Security Operations Centre (SOC) just isn't realistic.
For a more practical and cost-effective approach, many Canadian businesses are choosing to partner with an MSSP like CloudOrbis. This move lets you tap into a dedicated team of security professionals and top-tier technology without the huge upfront investment and ongoing overhead.
Partnering with an expert gives you immediate advantages:
This model lets your internal IT team get out of the weeds of constant security monitoring. They can finally focus on strategic projects that actually grow the business, all while knowing your endpoints are being protected by specialists. It’s a clean solution to the skills gap and alert fatigue that plague so many in-house teams.
To see how this works in practice, you can learn more about our security managed services and how we protect businesses just like yours.
When business leaders start looking into Endpoint Detection and Response, a few common questions always come up. Getting clear, straightforward answers is the key to making a confident, informed decision for your cybersecurity strategy. We’ve gathered the most frequent ones to clear up any confusion.
Not quite. While many modern EDR solutions include next-generation antivirus (NGAV) features, they really serve two different, vital roles. Antivirus is all about prevention—it’s designed to block known threats before they can do any damage. EDR, on the other hand, is built for detection and response after a threat has slipped past your initial defences.
Think of it this way: your antivirus is the lock on your front door. EDR is the security camera system and the response team that shows up when someone breaks a window. They work best together. EDR assumes a breach is always possible and gives you the tools to find and neutralize it, a capability that traditional antivirus just doesn't have.
This is a big concern, and for good reason. Managing an EDR tool effectively in-house can be incredibly complex and time-consuming, which is a real challenge for most mid-sized businesses. The system produces a massive amount of data that needs skilled security analysts to interpret and act on 24/7.
This is exactly why a Managed Detection and Response (MDR) service is the perfect fit. When you partner with a managed provider, you get all the power of advanced EDR protection without the overwhelming operational burden. It makes top-tier security accessible and effective for a company of any size.
In Canada, compliance regulations like PIPEDA require businesses to prove they are actively protecting sensitive personal information. EDR isn't just a good idea for security; it's a critical tool for meeting these legal obligations.
Its main functions directly support your compliance efforts by:
Ultimately, EDR gives you the verifiable proof that you’re not just trying to stop breaches but are fully prepared to handle them if they happen—a cornerstone of modern data protection laws.
Ready to secure your endpoints without the in-house complexity? CloudOrbis Inc. provides expert-managed EDR solutions that protect your business around the clock, letting you focus on growth with confidence. Discover our advanced cybersecurity services at https://cloudorbis.com.

June 10, 2026
Unlock Insights: Analytics and Reporting for SMBs 2026Unlock growth with strategic analytics and reporting. Our guide helps Canadian SMBs turn data into actionable insights for compliance & ROI.
Read Full Post
June 9, 2026
Cloud Security Posture Management: SMB Guide 2026Understand cloud security posture management (CSPM) essentials for Canadian SMBs. Our 2026 guide covers vital features, common risks, and how to begin.
Read Full Post
June 8, 2026
What Is IT Vendor Management? a Guide for Canadian SMBsLearn what is IT vendor management, its lifecycle, benefits, and risks. Our guide for Canadian SMBs covers best practices for security and compliance.
Read Full Post