June 9, 2026
Cloud Security Posture Management: SMB Guide 2026Understand cloud security posture management (CSPM) essentials for Canadian SMBs. Our 2026 guide covers vital features, common risks, and how to begin.
Read Full Post%20(1).webp)
Usman Malik
Chief Executive Officer
April 25, 2026
A clinic owner gets a questionnaire from a payer, a security checklist from a software vendor, and an urgent note from staff about shared inboxes all in the same week. The question sounds simple. Do we have a HIPAA risk assessment? In practice, that question reaches into systems, workflows, vendors, training, and the decisions people make under pressure every day.
For Canadian SMBs, a hipaa risk assessment checklist works best as a how-to process, not a form to complete and file away. The useful version shows how to find risk in the tools you already use, how to document it in a way that stands up to scrutiny, and how to connect each issue to a realistic fix. That includes knowing when an internal team can handle the work and when it makes sense to bring in an MSP for support. If your infrastructure records are incomplete, start with an IT infrastructure checklist for small and mid-sized businesses before you assess compliance gaps.
The Canadian context changes the work. A private clinic in Ontario may use a U.S.-based EHR, Microsoft 365, outsourced billing, and a scanning process for intake forms. HIPAA may be part of the requirement set, but it is rarely the only one. Provincial privacy obligations, retention practices, and data residency expectations can shift the scope quickly. A checklist that ignores that reality can leave leadership with a false sense of coverage.
That is why this guide focuses on execution. Each step breaks the assessment into manageable tasks, uses examples drawn from clinics and other SMB environments, and ties findings to practical next actions. Some of those actions are technical, such as tightening access control or reviewing backups. Others are operational, such as fixing document handling practices or reviewing modern healthcare document management processes that expose PHI outside the core EHR.
If secure communications are part of your current review, pair this article with a complete security guide for HIPAA email compliance.
A clinic can spend weeks discussing HIPAA risk and still miss the place where PHI leaks. I see this early in assessments. Leadership names the EHR, backup system, and firewall, but no one mentions Teams chat exports, scan-to-email workflows, personal phones, archived PST files, or the billing tool one department bought on its own.
Start with a direct question. Where does PHI get stored, viewed, sent, copied, printed, transcribed, or backed up? That scope is wider than many SMBs expect, especially in Canadian environments where a U.S.-hosted application may sit alongside Microsoft 365, local file shares, paper records, and provincial record-handling requirements.
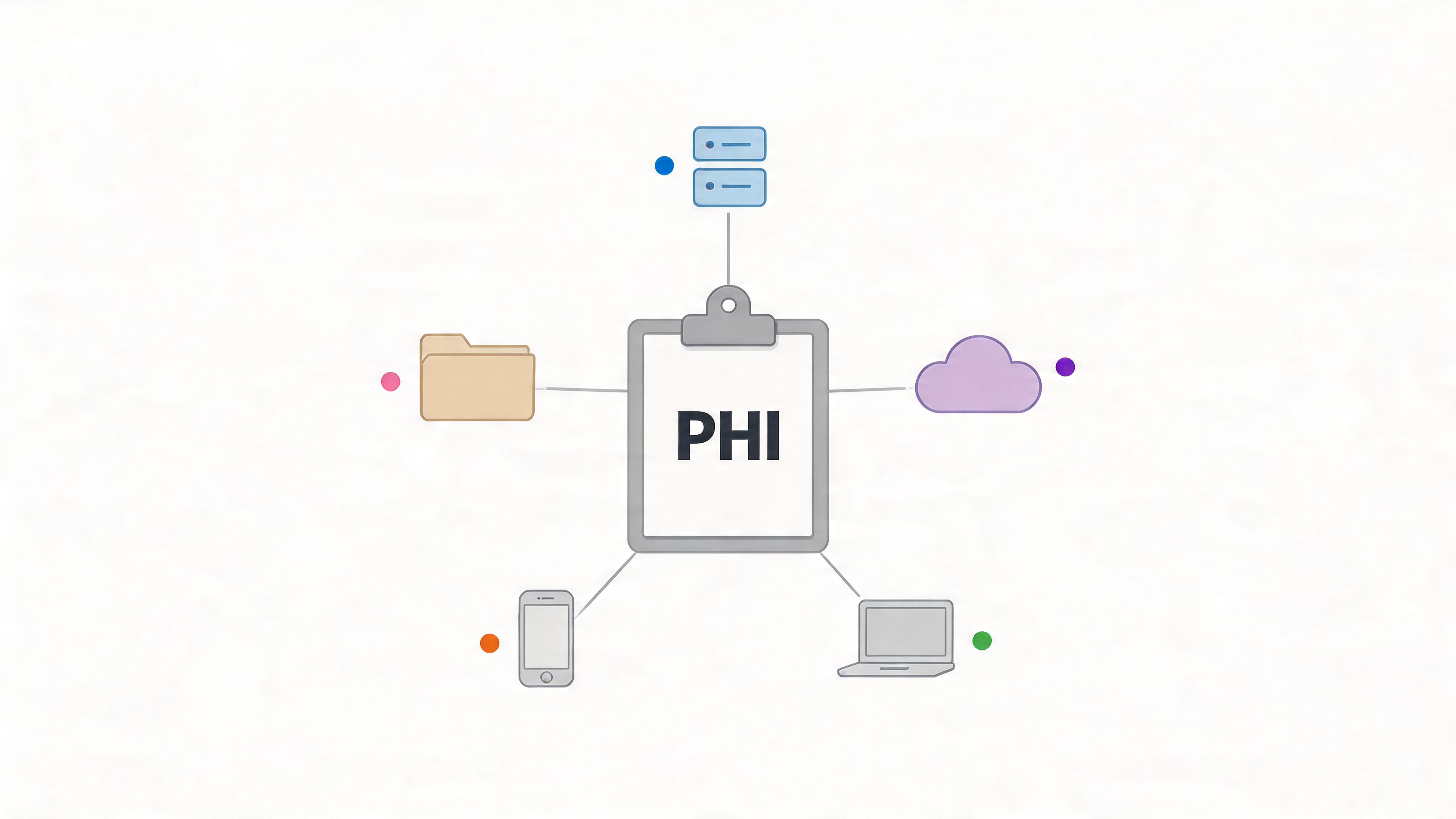
Use a spreadsheet if that is what your team can maintain. The format matters less than the coverage. Pull system names and device records from your firewall, endpoint tool, Microsoft 365 admin centre, backup console, cloud app list, and any existing asset register. Then test that list against reality by speaking with department leads, front-desk staff, finance, and anyone who handles intake, referrals, or reporting.
That second step matters. Technical tools show what is connected. Staff conversations reveal what is actively used.
Document four things for every item:
For Canadian SMBs, the work transitions from theoretical to practical. An Ontario clinic may find referral forms scanned to a shared mailbox, then saved to SharePoint and copied into the EHR. A dental office may discover appointment reminders include PHI in a third-party SMS platform. A manufacturer with an occupational health program may realize employee medical files sit inside an ERP module that was never reviewed by IT or compliance.
Cloud services need their own line items. Do not record Microsoft 365 as a single entry and move on. Exchange Online, SharePoint, OneDrive, Teams, Intune, Entra ID, and backup tools each create different risks, permissions, and retention questions. The same goes for cloud file-sharing apps, e-fax services, transcription platforms, and AI note tools.
Practical rule: If a system can send, store, sync, transcribe, print, back up, or export PHI, put it in the inventory.
Shadow IT usually shows up here. So do the awkward trade-offs. Staff often adopt quick workarounds because the approved process is slow, clunky, or unavailable after hours. The answer is not just to shut tools down. First identify what problem staff were trying to solve, then decide whether to secure the current process, replace it, or remove it.
If your records are incomplete, start by tightening the basics with this IT infrastructure checklist from CloudOrbis. If the environment includes internet-facing systems, remote access, or cloud apps with uncertain exposure, a review of penetration testing services for healthcare and SMB environments can help confirm whether your inventory matches real attack paths. Teams dealing with file sprawl and mixed paper-to-digital workflows should also review modern healthcare document management.
Keep this inventory as a living record. It should change when a vendor is added, a workflow moves to the cloud, a device class is retired, or a department starts using a new tool. That record becomes the foundation for every step that follows.
Once you know where PHI lives, shift from inventory to exposure. At this stage, many businesses overfocus on ransomware and miss the boring weaknesses that provide access. Default credentials, stale admin accounts, broad SharePoint permissions, unsupported Windows systems, weak vendor access controls, and unsecured network closets cause plenty of trouble before any “advanced” attack shows up.
A useful threat list has three parts. What can go wrong, where it can happen, and why the current state allows it.

Technical vulnerabilities matter, but administrative and physical gaps often make them worse. A clinic can have MFA on most accounts and still carry high risk if legacy admin accounts are excluded. A file server can be patched and still leak PHI if staff export records to unmanaged laptops.
Document threats in categories so you don’t miss entire classes of problems:
A clinic might find an old Windows Server still running a patient database because a vendor never approved an upgrade. A construction company with occupational health files may discover an always-on VPN account with default credentials. A manufacturer may learn its backup data isn’t encrypted even though the production systems are.
Automated scans are valuable, but they won’t show everything. They won’t tell you that a receptionist can access folders meant for finance, or that a former contractor still appears in an admin group, or that staff regularly text appointment details from personal phones.
That’s why walkthroughs and targeted testing matter. If you need a deeper technical view, a structured penetration testing service review from CloudOrbis can help validate whether your identified weaknesses are exploitable in the production environment.
Good documentation beats dramatic language. Write down the weakness, the system, the potential outcome, and the likely fix.
A risk list gets useful when leadership can decide what needs funding, what needs a quick fix, and what can wait for the next review cycle. That requires two judgments for each issue. How likely is it, and what happens to the business if it does occur?
For most Canadian SMBs, a simple matrix works well. Score each item as low, medium, or high for likelihood and impact, then write down why. Consistency matters more than a complicated formula. If two people score the same issue differently, that usually points to a gap in context, not a scoring problem.
A technical weakness only matters if it creates a real business consequence. Start there. If a workstation in a clinic is left unpatched, does that expose patient records, interrupt appointments, delay billing, or force staff onto paper? If an M365 account lacks MFA, could an attacker reach email, Teams chats, and shared files that include health information?
Canadian SMBs often benefit from a more structured cybersecurity risk management process. The method should connect each technical finding to an operational outcome, a privacy obligation, and a practical remediation path.
A small medical clinic might score ransomware as high likelihood and high impact because even a short outage affects booking, chart access, and patient communication. A manufacturing firm with employee health files may score weak file-share permissions as medium likelihood but high impact because a single internal disclosure can trigger legal, HR, and reputational issues. A departing employee with broad access can look low likelihood on paper, yet still justify immediate action because the potential scope of misuse is too large to ignore.
For Canadian organisations, impact scoring should reflect more than a generic HIPAA worksheet. If the business handles personal health information in Ontario or another province with its own privacy rules, the consequences of a failure may include contractual issues, provincial reporting duties, and patient trust concerns at the same time.
That is why this checklist works best as a how-to guide, not just a list. The same control failure can carry different weight depending on the business. In a clinic, an exposed shared mailbox may affect appointment coordination and patient disclosures. In a cross-border service provider, the same issue may also raise data residency and consent questions. A US-focused template often misses that distinction.
Score each risk from three angles: operational disruption, privacy impact, and recovery effort.
Residual risk belongs in the discussion too. If encryption, MFA, backups, or logging already reduce the chance of harm, record that clearly. Leadership needs to see both the raw issue and the remaining exposure after current controls are taken into account. That makes prioritisation more defensible, especially when budgets are tight and every remediation item competes with an operational project.
Keep the output practical. For each risk, document the affected system, the reason for the score, the likely business consequence, the current safeguards, and the recommended next step. That turns the assessment into something a clinic manager, office administrator, or operations lead can use.
A clinic owner approves a security policy, assumes the basics are covered, and later finds out a former employee account still has access to shared files. That gap is what this step is meant to catch. The goal is to confirm that the controls you believe are in place are configured, enforced, and supported by documentation your team can follow.
Start with a side-by-side review of policy versus production. If your policy requires laptop encryption, check device compliance reports. If MFA is required, verify that service accounts, emergency admin accounts, remote access tools, and older mail protocols are not bypassing it. For Canadian SMBs, this is also the point to check whether privacy commitments made to clients, insurers, or provincial regulators match the way data is stored and accessed in Microsoft 365, line-of-business apps, and backup systems.
Review the controls that affect PHI most directly: access management, audit logs, endpoint protection, email security, backup and restore, remote access, incident response, media disposal, and physical safeguards.
Cloud environments need extra attention because the control points are spread across multiple admin consoles. In M365 alone, Exchange, SharePoint, Teams, OneDrive, Defender, Intune, Purview, and newer AI features all need separate review. If staff can use AI assistants or summarization tools, assess prompt handling, permission boundaries, retention settings, and DLP policies before those features become part of daily work.
This is often where smaller organisations identify the underlying issue. The control exists, but only partly.
A medical clinic may discover that MFA protects staff accounts but not a legacy scanner-to-email account. A legal office may find that its written standard requires encryption, while several partner laptops were never enrolled in device management. A business with a solid backup dashboard may only learn during testing that file recovery is slow, incomplete, or dependent on one administrator who is away when needed.
Policies and procedures should be current, approved, easy to find, and reflected in day-to-day work. A short password and access policy that maps to actual settings is more useful than a 20-page document nobody reads. The same applies to incident response, acceptable use, remote access, data retention, and termination procedures.
For a Canadian SMB, good documentation also helps answer practical questions that templates often miss. Which systems can store PHI outside Canada. Who approves that exception. What happens if a vendor uses AI features that process sensitive content. When should management call in outside help instead of troubleshooting internally.
Use evidence that stands up in an audit and helps your own team make decisions:
The trade-off is straightforward. Waiting for perfect documentation delays risk reduction. Updating controls without documenting them creates confusion later. The practical approach is to fix the highest-risk gaps first, then update the policies and procedures so they match reality.
If the business lacks the time or internal depth to test M365 controls, validate backups, review AI exposure, and clean up old policies, that is usually the point to bring in an MSP. A good partner should not just hand over a report. They should show what was checked, what failed, what to fix first, and which items your team can maintain on its own.
A receptionist forwards intake forms to a personal email so she can finish work from home. An office manager approves access for a temporary contractor without checking the request. A clinician pastes patient details into an AI prompt to save time. None of those incidents start with a failed firewall. They start with a staff decision.
That is why training needs to be reviewed as a working security control. A risk assessment should show who receives training, whether the content matches each role, how often it is updated, and what proof you keep when staff complete it.
Completion rates matter, but behaviour matters more.
Start with role-based coverage. Front-desk teams handle forms, scans, attachments, and identity checks. Clinical staff use mobile devices and remote access. Managers approve exceptions and often create risk without realising it. IT staff need deeper instruction on privileged access, logging, MFA, retention, and AI settings in Microsoft 365. If everyone gets the same annual module, the programme is easy to administer but weak in practice.
For Canadian SMBs, this is often where a generic HIPAA checklist falls short. A small clinic in Ontario may have solid privacy training for in-person care but no guidance for staff who work from home part of the week. A multi-site business may train payroll staff on confidentiality yet miss the fact that employee health information can trigger the same handling problems as patient data. The training review should connect policy to the systems and workflows your team uses.
Use realistic scenarios to test judgment. Ask staff what they would do if a patient sends records from a personal Gmail account, if a coworker asks for shared mailbox access "just for today," or if Copilot pulls sensitive content into a workspace with broad permissions. These examples show whether people understand the rule and can apply it under pressure.
Modern tools need their own section in training. If staff use Microsoft 365, Teams, SharePoint, OneDrive, or AI features, the training should cover prompt hygiene, file sharing boundaries, retention, approved use cases, and when to stop and ask for help. I have seen organisations roll out new M365 features quickly and assume the existing privacy module still covers the risk. It usually does not.
Measure the programme with evidence you can defend in an audit. Review policy acknowledgements, phishing simulation results, incident reports, repeat policy violations, and records of role-based sessions. If you need a stronger starting point, this cybersecurity training for employees guide outlines what practical security education should look like.
The trade-off is simple. Short, generic training is easier to deliver. Targeted training takes more effort, but it gives staff clearer decision rules and gives leadership better evidence that the control is working. If your team cannot build role-based content, test real-world scenarios, or update training to reflect M365 and AI use, that is usually the point to bring in an MSP to help structure the programme and document the results.
Most organisations have more vendors touching PHI than leadership realises. The EHR is obvious, but what about the backup provider, hosted VoIP platform, e-fax service, M365 consultant, payroll processor, transcription app, or outsourced billing partner? Every one of them changes your risk profile.
A proper vendor review starts with a vendor inventory and ends with documented evidence. If a third party creates, receives, maintains, or transmits PHI on your behalf, you need to understand what access they have, what protections they use, and what agreement governs that relationship.
The most common mistake is reviewing agreements without reviewing access, or reviewing access without updating contracts. Do both at the same time. Confirm whether the vendor has admin rights, direct PHI access, API connectivity, data export capability, or backup copies.
For Canadian SMBs with cross-border workflows, this gets more complex. The guidance in the verified data notes that Alberta clinics saw a rise in cross-border PHI audits after updated privacy guidance, and many checklists still fail to include vendor BAAs that align with both regimes. A generic HIPAA checklist rarely captures that nuance well.
A dental practice may realise its EHR vendor has been handling records for years without the right agreement in place. A law firm may learn its document platform stores data across jurisdictions without clear residency controls. A manufacturer may discover an HR vendor used a subcontractor that was never assessed.
Not every vendor will provide the same level of assurance. That’s normal. What matters is having a consistent review standard and documenting exceptions.
Vendors don’t all need the same scrutiny. A strategic IT provider with privileged access deserves a deeper review than a low-risk tool with no PHI exposure. The important thing is to stop treating all suppliers as equal.
An assessment without remediation turns into shelfware. The strongest teams convert findings into an execution plan within days, while the context is fresh and leadership still remembers why the work matters.
Your remediation plan should answer five questions. What’s being fixed, who owns it, what the target date is, what dependencies exist, and how you’ll verify completion. If any of those are missing, tasks drift.
Not every issue deserves the same response. Some need immediate action, such as disabling stale accounts, closing public sharing links, or enforcing MFA on excluded users. Others are bigger projects, like replacing unsupported servers, redesigning SharePoint permissions, or moving from ad hoc backups to a tested recovery platform.
A clinic might structure the plan in phases. First, lock down privileged access and close obvious sharing gaps. Next, remediate endpoint encryption and backup issues. Then tackle longer-term cloud governance and policy alignment. A legal practice may need a staged migration away from an insecure file share into a more controlled document environment.
Leadership support proves essential. If the plan names actions without assigning budget, owners, or dates, it won’t move.
Remediation has to fit the business. You can’t shut down a clinic for a week to rebuild every workstation. You may need evening cutovers, pilot groups, temporary compensating controls, and clear communication with staff.
One area that often gets missed is resilience. Security fixes reduce the chance of an incident. Recovery planning reduces the damage when one still happens. That’s why remediation planning should connect directly to business continuity and disaster recovery planning, especially for organisations that depend on access to records to operate safely.
A good remediation plan is readable in one sitting. If leadership can’t understand it, they won’t support it.
For internal teams building programmes around recognised security practice, foundational learning such as CISSP certification can also help frame risk treatment decisions more consistently.
A clinic passes its annual assessment, then six months later a new staff member gets broad access through a rushed onboarding change. No one notices. A second team starts sharing files from a cloud app that never went through review. The written assessment is still on file, but it no longer reflects how the business operates.
That is why monitoring and reassessment have to be built into normal operations.

For Canadian SMBs, continuous monitoring does not require a large enterprise platform. It requires visibility into the systems that would create the biggest operational and compliance problem if they drifted out of policy. Start with identity, endpoint protection, email security, privileged access, backups, audit logs, and cloud sharing activity.
Small changes create real exposure over time. A permission group gets reused for convenience. MFA is left off for one account tied to an old workflow. Backup alerts go to a mailbox nobody checks. Each issue looks minor on its own. Together, they create the kind of weakness that leads to an incident or a failed audit response.
The practical test is simple. If a doctor accessed records after hours from an unusual location, or if a law office suddenly opened a client folder to everyone in the firm, would someone know within hours, or only after a complaint, outage, or investigation?
A schedule only works if staff can follow it consistently. For most SMBs, I recommend a cadence that matches available time, internal skill, and the pace of change in the business.
A workable model often looks like this:
This is the part many teams underestimate. The hard part is not writing the schedule. The hard part is assigning owners, defining what gets reviewed, and deciding what triggers escalation.
Monitoring only helps if it leads to a response. If logs show repeated failed sign-ins, someone needs a defined next step. If a quarterly review finds inherited permissions on a shared drive, that finding needs an owner, deadline, and follow-up check. If a backup test fails, the issue belongs on the risk register, not in a forgotten ticket queue.
That is also where an MSP can add value. Internal teams are often stretched thin, especially in clinics, professional services firms, and growing multi-site businesses. A partner such as CloudOrbis can help set alert thresholds, review logs, run quarterly check-ins, and translate technical findings into business decisions leadership can act on.
The goal is straightforward. Keep the risk assessment current enough that it reflects the systems, staff, vendors, and workflows you have now, not the version of the business you had last year.
| Activity | Implementation complexity | Resource requirements | Expected outcomes | Ideal use cases | Key advantages |
|---|---|---|---|---|---|
| Conduct a Comprehensive Inventory of All Systems and Data | Medium–High (time‑intensive, cross‑department) | Asset discovery tools, CMDB, staff time, interviews | Complete inventory and data flow map for PHI locations | Organizations with mixed legacy/cloud systems or pre‑audit readiness | Identifies shadow IT, creates baseline for remediation |
| Identify and Document All Potential Threats and Vulnerabilities | High (specialized testing and analysis) | Vulnerability scanners, pen‑test tools, security experts | Detailed vulnerability list and exploitable attack vectors | After initial inventory or before major remediation projects | Reveals specific weaknesses and prioritizes fixes |
| Assess the Likelihood and Impact of Identified Risks | Medium (methodology and stakeholder input) | Risk scoring frameworks, threat intelligence, multi‑stakeholder input | Risk‑ranked inventory with likelihood × impact scores | Prioritizing remediation, budgeting, compliance justification | Aligns security priorities with business impact |
| Review Security Controls and Document Policies & Procedures | High (deep access, thorough validation) | Log access, configuration reviews, auditors, testing tools | Verified control effectiveness and policy‑practice alignment | Compliance audits, control validation, policy refresh | Exposes ineffective controls and reduces wasted spend |
| Conduct an Employee Risk and Compliance Training Assessment | Low–Medium (ongoing program evaluation) | Training platform, phishing simulations, HR tracking | Training completion metrics and behavior change indicators | Reducing human‑factor incidents, regulatory evidence | Strengthens human firewall and provides audit documentation |
| Evaluate Third‑Party Vendor and Business Associate Security | Medium (contractual and technical review) | Vendor inventory, BAAs, questionnaires, assurance reports (SOC 2) | Vendor risk profiles and verified contractual protections | Outsourced services, supply‑chain risk management | Transfers some liability and uncovers downstream risk |
| Develop a Risk Management and Remediation Plan | Medium–High (coordination, exec sponsorship) | Project management, budget, owners, KPIs | Prioritized action plan with timelines, owners, and success criteria | Post‑assessment remediation, long‑term risk reduction | Converts findings into accountable, trackable actions |
| Establish Continuous Monitoring and Regular Re‑assessment Schedule | High (ongoing operations and analysis) | SIEM/SOC, monitoring tools, analysts, recurring budget | Real‑time alerts, periodic audits, annual re‑assessments | Mature security programs, high‑risk regulated environments | Early detection, prevents security decay, continuous compliance |
A clinic finishes its HIPAA risk assessment and gets a clean spreadsheet of findings. Then Monday starts. Staff still need to see patients, invoices still need to go out, and someone has to decide whether the first priority is MFA rollout, backup testing, vendor contract cleanup, or fixing shared accounts in Microsoft 365. That is the point when visibility turns into ownership.
A useful hipaa risk assessment checklist needs to show how to act on each finding, not just how to record it. For Canadian SMBs, that matters because HIPAA work rarely sits in a neat U.S.-only box. Teams often deal with cross-border data flows, hybrid work, cloud apps, outsourced IT functions, and privacy obligations that overlap with Canadian requirements. A generic checklist can start the conversation. It usually does not tell a five-site clinic, a specialty practice, or a growing professional firm how to close gaps without disrupting operations.
The practical approach is to break the work into decisions leaders can assign and track. Inventory the systems and data that touch PHI. Document specific threats and weak points in the current environment. Rate risk in business terms, so leadership can see what needs attention first. Confirm that controls work as configured, on paper and in daily use. Review staff behaviour and vendor exposure as part of the same risk picture. Then convert the findings into a remediation plan with owners, due dates, and evidence requirements.
At this stage, many organisations decide whether compliance will remain an occasional project or become part of day-to-day operations. Small and mid-sized teams usually do not fail because they ignored security. They run into trouble because identity, endpoint management, cloud security, policy maintenance, training, backup validation, and vendor oversight sit with different people. If no one owns the full process, tasks drift and audit evidence gets harder to produce.
An experienced MSP can close that execution gap. The right partner should help define scope, run the assessment, explain findings in plain business language, implement fixes with limited disruption, and keep the review cycle on schedule. In practice, that often means dealing with the work internal teams postpone first, such as access reviews, M365 governance, device standards, backup recovery testing, and third-party security checks.
CloudOrbis is built for that role. As a Canada-based managed IT and cybersecurity partner, CloudOrbis helps organisations turn compliance from a reactive exercise into a stable operating function. That can include risk assessments, remediation planning, security hardening, employee awareness support, business continuity alignment, and ongoing monitoring backed by vCIO guidance. For healthcare providers and other businesses handling sensitive health information, that mix matters because compliance, uptime, and trust all depend on the same operational discipline.
If your current checklist feels incomplete, or if you are unsure your environment would hold up under an audit or incident review, now is a good time to tighten the process. A well-run assessment gives you clarity. A supported program gives you confidence.
If your organisation needs help turning a hipaa risk assessment checklist into a workable security programme, CloudOrbis Inc. can help assess your environment, prioritise the right fixes, and support ongoing compliance with managed IT, cybersecurity, cloud, and vCIO services designed for Canadian SMBs.
June 9, 2026
Cloud Security Posture Management: SMB Guide 2026Understand cloud security posture management (CSPM) essentials for Canadian SMBs. Our 2026 guide covers vital features, common risks, and how to begin.
Read Full Post
June 8, 2026
What Is IT Vendor Management? a Guide for Canadian SMBsLearn what is IT vendor management, its lifecycle, benefits, and risks. Our guide for Canadian SMBs covers best practices for security and compliance.
Read Full Post
June 7, 2026
Legacy System Modernization for Canadian SMBsUnlock growth with legacy system modernization. Our guide helps Canadian SMBs navigate strategies, costs, and risks for a smooth transition to modern IT.
Read Full Post