June 6, 2026
HIPAA Compliance Checklist: A 10-Point Guide for SMBsNavigate HIPAA with our comprehensive HIPAA compliance checklist for Canadian SMBs. Learn 10 actionable steps for safeguarding PHI and avoiding costly fines.
Read Full Post%20(1).webp)
Usman Malik
Chief Executive Officer
March 8, 2026
It only takes one employee clicking on one bad link to unravel your entire business. What starts as a simple mistake can quickly spiral into a multi-million-dollar disaster. This is why effective cybersecurity training for employees isn't just an IT expense—it's one of the most critical business strategies for survival and resilience you can have.

When we talk about cybersecurity, the conversation often defaults to firewalls, antivirus software, and other tech-heavy tools. And while those are absolutely essential, they can’t do a thing to stop a threat that an employee unknowingly invites right through the front door.
An untrained team member is the most common and unpredictable entry point for cybercriminals. This "human element" is exactly why so many medium-sized organizations—especially in sectors like manufacturing, healthcare, and legal services—have become such popular targets. They hold valuable data but often lack the massive security budgets of enterprise corporations, making them the perfect middle ground for attackers.
This threat isn't just an abstract concept; it has a very real and growing price tag for Canadian businesses. The latest data shows a startling trend: 44% of Canadian organizations reported a cyber-attack in the last year alone.
Even more alarming, the cost of recovery has exploded, doubling from $600 million in 2021 to a staggering $1.2 billion in 2023. This surge is happening because the attacks are getting more severe, even as the frequency has somewhat stabilized.
The numbers tell a tough story. Despite 73% of Canadian small and medium-sized businesses (SMBs) having been hit by at least one cyber-attack, a worryingly low 47% actually feel prepared to handle one.
The reality is clear: waiting to react to a breach is no longer a viable option. It’s a strategy that accepts catastrophic financial and reputational damage as inevitable. The only way forward is to build a resilient security culture from the ground up.
Investing in your people is the single most effective way to move from a reactive, damage-control mindset to a proactive one. When you give your team comprehensive cybersecurity training, you equip them to spot and report threats before they ever have a chance to do harm.
Think about it this way: a well-crafted phishing email is a test. Without any training, it’s a test your employees are almost guaranteed to fail. But with the right training, that same email becomes an opportunity for your team to actively participate in the organization's security.
A solid training program needs to build practical skills and awareness. We’re not trying to turn everyone into a security expert, but we do need to cover the essentials:
On top of that, threats are constantly changing. Today’s training must also prepare employees for new dangers, like understanding how to detect AI in video, audio, and text, which criminals are using to create incredibly convincing social engineering attacks. By focusing on these core areas, you directly address the most common ways attackers get in.
You can learn more about the common pitfalls we see by exploring some of the most crucial cybersecurity mistakes and how to stop them in our other guide.
Let's be blunt: a one-size-fits-all approach to cybersecurity training is a waste of time and money. It leaves your business just as vulnerable as before. Sending the same generic phishing module to your CEO and your warehouse coordinator completely misses the point. The simple truth is that risk isn't distributed evenly across your company.
A truly effective program starts by acknowledging this fact. It’s about building a curriculum tailored to the specific threats each employee actually faces in their day-to-day work. Forget about just ticking a compliance box. We need to create a continuous cycle of learning that turns security awareness from a yearly chore into a genuine business advantage.
First things first, you need to put on your detective hat and look at your organization department by department. Think about the data, systems, and tools each team uses daily. From there, you can map the most likely cyber threats they'll run into. Every role has its own unique risk profile.
For instance, your finance team is on the front lines, dealing with wire transfers and sensitive financial data. This makes them a top target for business email compromise (BEC) and sophisticated invoice fraud. Their training has to be laser-focused on verifying payment requests and spotting any communication that even hints at moving money.
Your marketing team, on the other hand, lives in a world of third-party apps, social media, and new software. Their biggest risks? Probably credential theft from a sketchy marketing tool or downloading malware that’s cleverly disguised as a new font or image file. Their training needs to hammer home the importance of vetting new tools and recognizing threats on the platforms they use all day.
A targeted curriculum acknowledges that the threat an accountant faces is vastly different from the one a sales representative encounters. By customizing the training, you arm each employee with the specific knowledge they need to defend against the attacks they are most likely to see.
Once you have your risk map, you can start building out a curriculum with specialized modules. This doesn't need to be some massive, complex project. Just start with a solid foundational course for everyone covering the basics, then layer on specific, short modules for different groups.
The human element remains a key factor in cybersecurity incidents across Canada. Ransomware, for instance, continues to be a top threat to our nation's critical infrastructure. In 2024 alone, the Canadian Centre for Cyber Security issued 336 pre-ransomware notifications to over 300 organizations, a proactive measure that helped avert up to $18 million in potential economic damage. This success highlights how trained staff who heed early warnings are instrumental in stopping attacks, a vital lesson for businesses in logistics, legal, and oil and gas. You can review the complete findings in the National Cyber Threat Assessment 2025-2026.
A single training session is like a crash diet—the results rarely last. If you want to create real, lasting behavioural change, security education has to be woven into the very fabric of your company culture through regular, bite-sized activities. For anyone looking to make their training more effective, checking out some practical online course tips can really boost how much your team engages and remembers.
Think beyond the initial onboarding. Run monthly phishing simulations that give immediate feedback to anyone who clicks. Share weekly security tips in your company's Teams or Slack channels. Make a big deal out of it and celebrate the "catches" when employees report real phishing emails—turn them into security champions.
By making cybersecurity an ongoing conversation, you change the perception from a one-time chore to a shared responsibility. This approach is particularly effective for organizations managing complex compliance needs, like those requiring LMS support for Alberta private career colleges. When your team understands the specific part they play in the company's defence, they stop being a liability and become your single greatest security asset.
You’ve designed a great curriculum, but a plan on paper is just that—a plan. The real test comes when you roll it out to your team. This is where your strategy becomes a living, breathing part of your company’s defences. Success hinges on how you deliver the training and, just as importantly, how you automate the process to keep it consistent and manageable.
This is where the rubber meets the road. The first big decision is how you'll get the content to your people. This choice impacts everything from employee engagement and scheduling to your budget. There's no single right answer, but for most medium-sized businesses, a blended approach works best.
Your company’s culture and day-to-day operations should guide your decision. A manufacturing firm with employees on the shop floor has very different needs than a law firm where everyone is at a desk.
To help you decide, here’s a look at the most common training formats and where they shine.
For most businesses we work with, the sweet spot is a mix: on-demand modules for the basics, followed by periodic live webinars or workshops for high-risk topics or emerging threats. This gives you flexibility while ensuring you can still get everyone together for critical, interactive sessions when it really counts.
This whole process—from risk mapping to role-specific modules and ongoing learning—should work like a well-oiled machine.
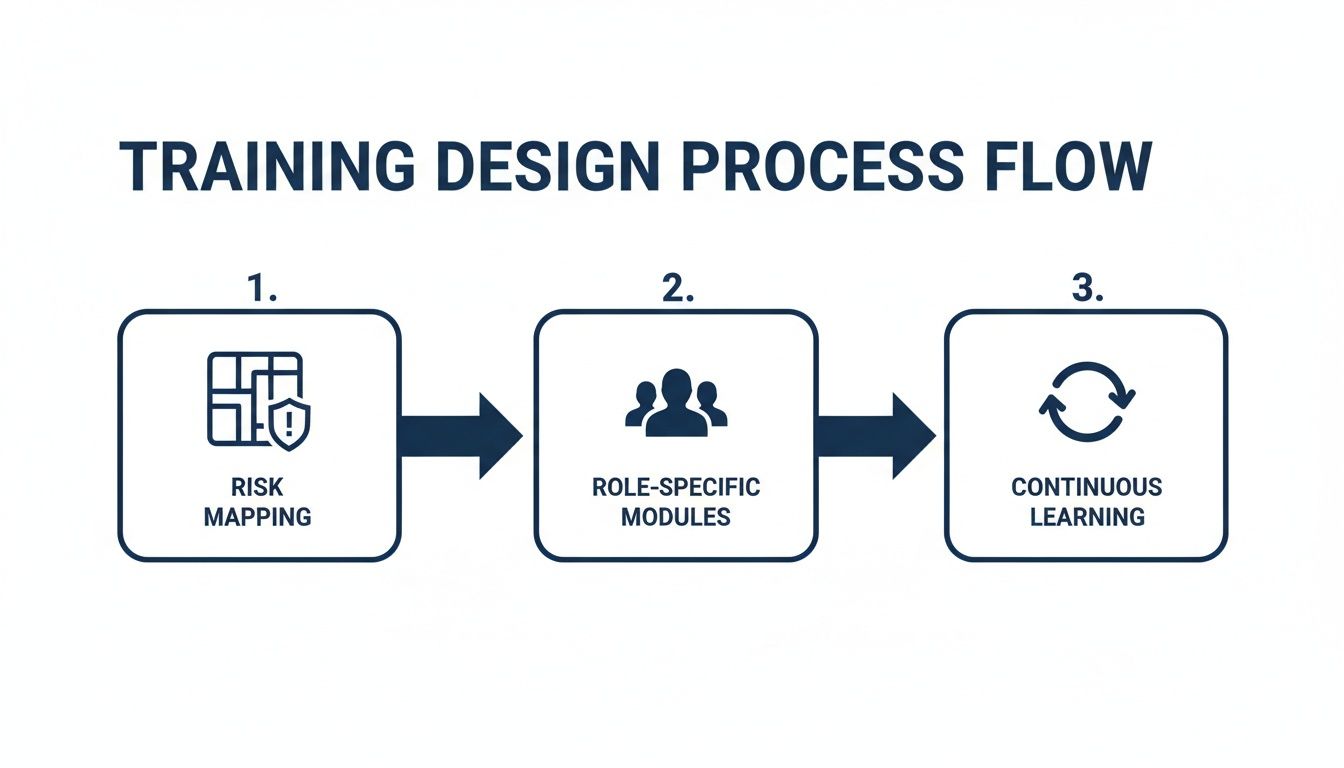
It’s not a one-time event. It’s a continuous loop where the insights you gain from one stage directly inform the next, keeping your program sharp and relevant.
When it comes to practical tools, phishing simulations are the single most powerful one in your cybersecurity training for employees toolkit. They give your team a safe space to practice spotting and reporting threats before a real one hits their inbox.
But here’s the thing: if you run them poorly, they can feel like a "gotcha" game that alienates the very people you’re trying to help.
A successful simulation program isn't about tricking employees; it's about building muscle memory. The aim is to make spotting and reporting suspicious emails an automatic, confident reflex rather than a moment of panic and uncertainty.
So, how do you get it right?
First, start simple and build up. Your initial simulation shouldn't be some impossibly clever attack. Begin with common phishing emails that are easier to spot, then gradually introduce more sophisticated tactics as your team gets better.
Next, provide immediate, constructive feedback. The moment an employee clicks a simulated phishing link, they should land on a page explaining exactly what happened. This page needs to clearly point out the red flags they missed and reinforce the correct action: reporting the email. That instant feedback is where the real learning happens.
Finally, celebrate the reporters. Don't just focus on who clicked. Make a point to actively praise employees who correctly identify and report the simulations. This positive reinforcement transforms the culture from one of fear to one of pride in actively defending the company.
This kind of hands-on practice delivers real results. We worked with a medium-sized Canadian manufacturing firm that was struggling with employees frequently clicking on malicious links. After implementing a program of regular, automated phishing simulations with immediate feedback, they saw their click rate drop by over 80% in just one year. They turned a major weakness into a strength by giving their team a safe way to practice.
Automating these simulations and the follow-up training is what makes a program like this sustainable. You can also find huge efficiencies with the right IT process automation software, which helps take repetitive IT tasks off your plate. By automating the delivery and tracking of your cybersecurity training for employees, you ensure it gets done consistently without becoming an administrative nightmare.

Reading about cybersecurity threats is one thing, but it’s not enough to stop a real attacker. Your team can know all the theory in the world, but nothing prepares them like the jolt of seeing a cleverly faked CEO request for a wire transfer hit their inbox. This is where you have to move from passive learning to active defence with hands-on training.
The goal here is to build muscle memory. When employees can practice spotting and reacting to threats in a safe, controlled environment, their responses become instinctual. Good security should be a reflex, not a research project during a crisis.
The push for practical skills isn't just a good training strategy; it's a response to a real economic challenge in Canada. As our digital economy grows, the demand for cybersecurity talent is blowing past the available supply. For a smart organization, this is a huge opportunity.
The Canadian Occupational Projection System (COPS) expects about 15,900 new job openings for Cybersecurity Specialists between 2024 and 2033. But with only around 18,700 job seekers projected to fill those roles, it’s clear we’re heading for a labour shortage.
By investing in hands-on cybersecurity training for employees, you do more than just bolster your own defences. You start building the talent you need from within your existing team. This is a critical issue, as detailed in reports on how Canada's IT sector needs skilled professionals ready to make an impact.
To build skills that hold up under pressure, you need to get more creative than slideshows and multiple-choice quizzes. It's time to create immersive experiences that force employees to apply what they’ve learned.
Effective hands-on training doesn't just test knowledge; it builds confidence. It gives employees the experience of successfully navigating a security threat, proving to them that they are capable defenders of the organization.
Here are a few powerful methods to bring your training to life:
Let's make this practical. Imagine you run a medium-sized legal firm in Calgary. A data breach exposing sensitive client information would be catastrophic, destroying your reputation and inviting massive regulatory fines.
A standard training module on data privacy is fine, but a breach simulation makes that risk feel real.
You could stage a drill where a senior partner’s email account is "compromised." This event would trigger a cascade of alerts and actions: fake client data is "leaked," and suspicious login notifications are sent.
The whole point is to test your team’s response in real-time:
Running this drill will instantly show you where the gaps are in your process and who needs more training. It’s a powerful, practical exercise that prepares everyone for a real crisis. This proactive approach works hand-in-glove with technical security measures, like formal penetration testing services, by making sure your people are as ready as your technology.
Investing in cybersecurity training for your employees just feels like the right thing to do, but how do you actually prove it's working? To keep the budget approved and the executives on board, you need to show a clear return on that investment. This means looking past simple metrics like course completion rates and digging into the numbers that show real, tangible changes in how your people behave.
A great training program does more than just tick a compliance box—it actively shrinks your organization's risk profile. Measuring that reduction is how you prove its worth. You need to be tracking KPIs that show your team is getting smarter and faster at spotting threats before they can do any harm. This data also gives you a roadmap for continuously improving the training itself.
Forget tracking how many people finished a module. That tells you nothing about whether the lesson actually stuck. Instead, pour your energy into these action-oriented metrics that paint a much clearer picture of your security posture.
These three KPIs are the foundation of a measurement strategy that means something. They shift the focus from passive learning to active participation—which is exactly what you want.
You can't improve what you don't measure. When you start tracking behavioural KPIs, your training program transforms from a simple expense into a measurable security control. The data will clearly show leadership how a small investment in your people is preventing multi-million-dollar mistakes.
To make all this data easy to digest and act on, you need a simple dashboard. This doesn't have to be some complex business intelligence tool; a shared spreadsheet or a built-in feature of your training platform works perfectly. The goal is to see trends at a glance and share progress with stakeholders.
Here’s a sample of what that could look like:
This dashboard becomes your command centre. If you see the phish-prone percentage creeping up in a specific department, like marketing, it’s a clear signal that their current training isn't hitting the mark. Maybe the simulations are too generic and don't reflect the spear-phishing attacks they're most likely to face. Now you have the data to justify deploying a more targeted module just for that team.
This data is also your most powerful tool for communicating with leadership. When you can walk into a budget meeting and show a chart where the phish-prone percentage has plummeted by 86% over the year, the conversation changes completely. You’re no longer just asking for training money; you're presenting hard evidence of a fortified defence that is actively protecting the business.
This is how you demonstrate a clear, undeniable ROI. It's a strategic approach that aligns perfectly with the broader advantages you can gain when you partner with an expert team, and you can explore more about the benefits of managed IT services in our dedicated article.
Even with the best playbook, questions are bound to come up when you’re about to launch a cybersecurity training program for employees. Business leaders, rightfully, want to know what they’re getting into—the real costs, the time commitment, and whether it will actually work.
Let's clear up some of the most common questions we hear from businesses just like yours.
This is usually the first question on everyone's mind. The short answer is: it depends, but it's always far less than the cost of a data breach.
A good rule of thumb is to budget between $100 to $200 per employee, per year. This range generally gets you access to a solid training platform, complete with on-demand courses, ongoing phishing simulations, and performance reporting.
For a business with 100 employees, that works out to about $10,000 to $20,000 annually. When you weigh that against the multi-million-dollar price tag of an average data breach, the investment makes perfect sense. The best return on investment is the disaster you never have to deal with.
The old-school, "one-and-done" annual training session just doesn't cut it anymore. For security habits to stick, the training needs to be a continuous part of your company culture, not a single event on the calendar.
Think of it as an ongoing conversation. A modern, effective schedule looks more like this:
This bite-sized, frequent approach respects your employees' time and keeps security top-of-mind, which is far more effective than an overwhelming, day-long session.
While every single person is a potential target, the risk isn't spread evenly across an organization. Some roles are simply targeted more often or are more susceptible to certain attack types.
For instance, we often see employees in marketing and sales with higher click-rates on phishing tests. This makes sense—their jobs require them to open attachments and click links from unfamiliar contacts all day long.
It's a huge misconception that only junior staff fall for scams. C-suite executives are prime targets for highly personalized "spear-phishing" attacks. Because of their authority and high-level access, a successful breach at the executive level can cause catastrophic damage.
A smart cybersecurity training for employees program recognizes these different risk profiles. The goal isn’t to point fingers, but to provide extra support where it's needed most.
This is a completely valid concern. In fact, it's one of the main reasons training programs fail. If the content is dry, generic, or feels like a mandatory chore, your team will mentally check out, and nothing will be learned.
The trick is to make the training engaging, relevant, and even a little fun.
Here are a few ways to beat training fatigue:
When you deliver training that respects your team's time and intelligence, you'll see engagement and retention soar.
At CloudOrbis, we believe a well-trained team is your single most valuable security asset. Our managed IT services include comprehensive employee training programs designed to turn your people into a proactive line of defence. Protect your business and empower your team by visiting us at https://cloudorbis.com.
June 6, 2026
HIPAA Compliance Checklist: A 10-Point Guide for SMBsNavigate HIPAA with our comprehensive HIPAA compliance checklist for Canadian SMBs. Learn 10 actionable steps for safeguarding PHI and avoiding costly fines.
Read Full Post
June 5, 2026
Serverless Architecture for Canadian SMBs: Guide 2026Practical guide to serverless architecture for Canadian SMBs. Learn benefits, costs, security, & migration tips. Migrate with confidence in 2026.
Read Full Post
June 4, 2026
IT Asset Management: A Guide for Canadian SMBsLearn how effective IT asset management can boost security, control costs, and drive growth for your Canadian SMB. A practical guide to getting started.
Read Full Post