June 5, 2026
Serverless Architecture for Canadian SMBs: Guide 2026Practical guide to serverless architecture for Canadian SMBs. Learn benefits, costs, security, & migration tips. Migrate with confidence in 2026.
Read Full Post%20(1).webp)
Usman Malik
Chief Executive Officer
November 29, 2025
Penetration testing is a controlled, simulated cyberattack against your organization, conducted by certified security experts. This process, often called ethical hacking, is designed to find and fix security vulnerabilities before a malicious attacker can exploit them. As a fundamental component of any modern cybersecurity strategy, it provides a real-world assessment of how your defences perform under pressure.

Imagine your business’s digital infrastructure is a new bank vault. You have installed alarms, thick steel walls, and complex locks. A basic vulnerability scan is like walking around to ensure all the doors are locked. While a good first step, it provides limited insight.
Penetration testing, on the other hand, is like hiring professional safecrackers to actively attempt a break-in. They will probe the walls for weak spots, check ventilation systems for entry points, and might even try to trick an employee into handing over the keys. The key difference is that penetration testing goes far beyond automated checks, using human creativity and intelligence to uncover subtle, complex security flaws that a simple scan would miss.
Professional penetration testing services act as a fire drill for your cybersecurity. The goal is not to cause a fire but to observe how your systems—and your people—react under the pressure of a realistic attack. This proactive approach allows you to identify and remedy weaknesses in a safe, controlled environment before they lead to a real disaster.
This process helps business leaders get clear answers to critical questions, such as:
By simulating an attack, you gain an invaluable attacker's-eye view of your security posture. This perspective, which automated tools alone cannot provide, shifts your strategy from merely reacting to threats to proactively building resilience.
Ultimately, partnering with a provider of comprehensive cybersecurity services that include penetration testing gives you a clear, actionable roadmap for strengthening your defences. It helps you prioritize your security budget, meet compliance requirements, and build trust with clients by demonstrating a serious commitment to protecting their data.
Penetration testing is not a one-size-fits-all service. The appropriate test depends on what you need to protect and the security questions you need to answer. Each variation targets different assets and potential weak points, providing a clear picture of your unique operational risks.
Consider it like a home inspection. You would not just check the front door; you would want an expert to examine the windows, roof, foundation, and internal alarm systems. Similarly, a thorough security assessment examines your business from every possible angle—from your external-facing presence to threats that may already be inside your network.
This is often the first test a business conducts. It simulates an attack from an outsider with no special access or internal knowledge, mimicking how most real-world cyberattacks begin. The ethical hacker acts as a digital scout, probing your internet-facing perimeter for any vulnerability they can exploit.
The main goal is to find and breach vulnerabilities in your external hardware and software, such as:
This test answers a critical question for any business leader: How well do our defences hold up against an anonymous attacker online? It is the essential starting point for understanding your security posture.
While external threats get a lot of attention, statistics consistently show that a significant number of security breaches originate from inside an organization. An internal penetration test simulates what a malicious insider—such as a disgruntled employee or an attacker using stolen credentials—could accomplish once they are past the perimeter.
Testers are given the same basic access as a typical employee. From there, they attempt to escalate their privileges to gain control of sensitive data or critical systems. This test highlights weak internal controls, poor network segmentation, and flawed access policies, revealing the potential damage from a single compromised account.
An internal test shifts the focus from keeping attackers out to containing them if they get in. It is a crucial part of building a 'defence-in-depth' strategy, ensuring one compromised laptop does not bring down the entire company.
If your business relies on web applications for sales, customer support, or daily operations, this test is non-negotiable. It involves a deep, focused dive into the security of a specific application, searching for common yet devastating flaws like SQL injection, cross-site scripting (XSS), and broken authentication.
An application test verifies whether your own software could be used to steal sensitive customer data, financial records, or valuable intellectual property. With web-based attacks remaining a top source of data breaches, securing your applications is vital for protecting both your bottom line and your reputation.
Wi-Fi is convenient, but it is also a common entry point for attackers, often due to simple misconfigurations or weak security. This test focuses exclusively on your wireless infrastructure, identifying vulnerabilities that could allow an unauthorized user to gain access to your corporate network.
During a wireless test, ethical hackers will attempt to:
This is especially important for businesses with large physical footprints like offices, warehouses, or clinics, where secure wireless access is essential for operations.
Cybersecurity is not just about technology; it is also about people. Social engineering tests measure how well your team withstands psychological manipulation, using tactics like phishing emails, pretexting (creating a believable but fake scenario), and baiting. These simulations reveal how easily an attacker could trick an employee into giving up a password or granting access.
While digital security is key, the physical world still matters. This is where services like physical penetration testing are valuable. These assessments check your physical security controls to determine if an unauthorized person could simply walk into a server room or access a restricted office area. This holistic view ensures every potential entry point—digital and physical—is secure.
To help you decide where to start, here is a quick guide matching the test type to the business risk it addresses.
This table helps connect each type of penetration test to the specific business question it is designed to answer, helping you prioritize based on your biggest concerns.
Choosing the right test, or a combination of them, ensures your security budget is spent wisely, tackling the risks that pose the greatest threat to your operations.
A professional penetration test is not a chaotic, unpredictable attack. It is a carefully structured project—a collaborative journey we take with you to uncover vulnerabilities in a controlled and methodical way. This approach demystifies the entire engagement, showing how it flows from an initial conversation to a final, actionable report that genuinely strengthens your security.
The entire process is built on a foundation of clear communication and agreed-upon rules. This is key to ensuring the testing is both thorough and safe, delivering maximum value without disrupting your daily operations. Each phase builds logically on the last, providing a clear roadmap for tangible security improvements.
The infographic below shows how a typical test flows, moving from your external defences through to internal systems and the specific applications you rely on.
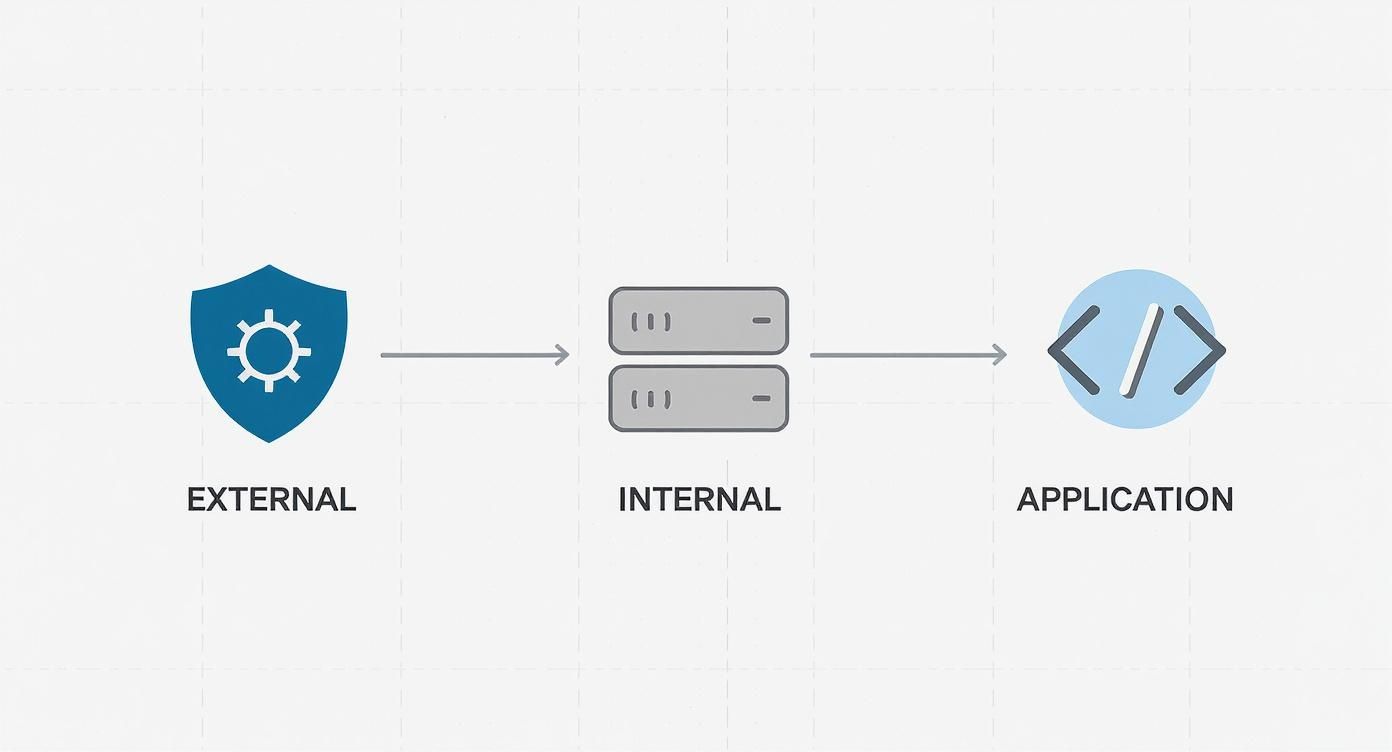
This visual highlights how a comprehensive assessment examines every layer of your digital environment, ensuring no potential entry point is missed.
This is arguably the most critical phase. Before any test is run, we work closely with you to define the scope and the rules of engagement. Think of it as drawing up a map and setting the ground rules for a military exercise.
We will clearly outline what is in-scope (the systems, applications, or networks to be tested) and, just as importantly, what is out-of-scope (anything that should not be touched). This collaborative planning ensures the test aligns perfectly with your business goals and risk priorities, focusing our efforts where they matter most. We also establish clear communication protocols and testing windows to avoid any impact on your business.
Once the scope is finalized, our ethical hackers begin the reconnaissance phase. Here, they start thinking and acting just like a real attacker would, gathering as much publicly available information about your organization as they can. This is not just a quick web search; it is a deep dive into your digital footprint.
They might look for information such as:
This intelligence-gathering stage is crucial. It helps our testers identify potential targets and map out their attack strategy, mimicking the exact preparation an adversary would undertake.
Now we move to the active testing phase. This is where our ethical hackers attempt to exploit the vulnerabilities they have identified. It is important to stress that this is a controlled and safe process. The goal is not to cause damage but to prove that a vulnerability is real and can be exploited.
The objective of exploitation is proof, not destruction. By successfully (and safely) breaching a defence, testers confirm a genuine risk that needs to be addressed, moving it from a theoretical problem to a documented business risk.
If a tester gains access, they will see how far they can go—a process we call post-exploitation. They might try to escalate their privileges to gain administrator rights or move laterally across the network to access other systems. This helps determine the true business impact of a single breach.
The final phase is where the true value of penetration testing services really shines. You receive a detailed report that goes far beyond a simple list of problems. A high-quality report is a strategic document that translates technical findings into clear business risks.
It will always include:
This report becomes your blueprint for security improvement. For businesses seeking guidance on turning these findings into a long-term strategy, exploring options like cybersecurity consulting can provide the expert support needed to build a more resilient security program. The test does not end with a list of problems; it ends with a clear path forward.
For many Canadian businesses, penetration testing is not just a security best practice—it is a mandatory legal and regulatory requirement. Failing to meet these obligations can trigger severe financial penalties, disrupt operations, and damage the trust you have built with customers.
This makes the connection between penetration testing and compliance critically important.
Think of it this way: a penetration test report provides tangible proof that you are conducting due diligence to protect sensitive information. It offers third-party validation that your security controls are not just in place but can also withstand real-world attack techniques. This is precisely the kind of documented evidence auditors and regulators expect to see.
Several major regulations either directly require or strongly imply the need for regular penetration testing. If your business operates in certain industries, these standards are non-negotiable.
Here are a few key regulations you may encounter:
While meeting compliance targets is a significant motivator, viewing penetration testing as merely a box to tick misses the point. These regulations exist for a reason: to keep sensitive data from being stolen and misused. A data breach can lead to more than just a compliance fine; it can cripple your company's reputation and lead to costly lawsuits.
The real value of compliance-driven penetration testing is that it fosters a proactive security mindset. It shifts the focus from merely satisfying an auditor to genuinely safeguarding the data your customers and partners have entrusted to you.
Investing in regular testing is an investment in business continuity and trust. The findings from a test provide a clear, prioritized roadmap for strengthening your defences, ensuring you are not only compliant but also genuinely resilient. This proactive approach helps build a security-first culture where protecting data is a core part of the business, not an afterthought.
By incorporating regular, thorough testing into your security program, you turn compliance from a burden into a strategic advantage. You can confidently tell clients, partners, and regulators that you are taking every necessary step to protect their information. This commitment is fundamental to operating responsibly and building a sustainable, trustworthy business. To see how these requirements fit into a broader strategy, it's helpful to explore comprehensive compliance solutions that align security practices with your specific industry mandates.
Choosing the right security partner is a critical decision for any business leader. The right firm provides a clear, practical roadmap to a stronger security posture. The wrong one can leave you with a false sense of security built on superficial checks. Making a smart choice here means your investment will effectively reduce real-world risk.
The market for penetration testing services is booming. In North America alone, it generated USD 755.9 million in revenue in 2023, which indicates two things: demand is high, and the field is crowded. You can dive deeper into market trends with the full analysis from Grand View Research.
This growth gives you plenty of options, but it also means you need a solid plan to distinguish true experts from the rest.
One of the first things to clarify is the difference between a real penetration test and a simple vulnerability scan. An automated scan is a useful starting point—it flags known issues like unpatched software. But that's where it ends. Think of it like a spell-checker; it catches obvious errors but has no understanding of the context.
A true penetration test, however, is driven by the deep, manual analysis of a skilled ethical hacker. This human element is crucial. An expert tester uses creativity and experience to chain together seemingly low-risk vulnerabilities, bypass security controls, and show you exactly how a real attacker would compromise your systems. They provide the critical context that a scanner cannot.
When you're speaking with a potential partner, ask them how they balance automated tools with manual testing. If they lean too heavily on automation, that is a significant red flag, as it often points to a less thorough, one-size-fits-all service.
To find a partner who will bring real value, you must push past the sales pitch. Your evaluation should focus on a few core questions that reveal the quality of their team, their process, and the reports they deliver.
A modern security strategy should align with essential penetration testing best practices. Use these questions to ensure any partner you consider is on the same page:
What methodologies do you follow? Top-tier firms build their tests on established frameworks like the MITRE ATT&CK framework, OWASP Top 10 for web applications, or the Penetration Testing Execution Standard (PTES). This demonstrates a structured, repeatable, and industry-respected approach.
What certifications and experience does your testing team hold? Look for credentials that require intensive, hands-on exams. Certifications like the Offensive Security Certified Professional (OSCP), CREST, and GIAC Penetration Tester (GPEN) are strong indicators that a tester has proven real-world skills.
Can you provide a sanitized sample report? The final report is the most important deliverable. It needs to be crystal clear, with a non-technical executive summary for leadership and detailed technical findings with actionable remediation steps for your IT team. If the report is confusing or vague, it's best to look elsewhere.
How do you handle post-engagement support and retesting? A great partner does not just email a PDF and disappear. Ask about their process for helping your team understand the findings, prioritize fixes, and—crucially—verify that your remedies have worked.
By asking these direct questions, you can cut through the marketing fluff and find a provider with genuine expertise. The goal is not just to check a compliance box; it is to find a true partner committed to making your organization more secure. Your investment in penetration testing services should empower you to build a more resilient business.
When you seek penetration testing services, you are not just hiring a vendor—you are choosing a security partner. At CloudOrbis, we view a penetration test as the beginning of a relationship, not a one-off project. We are committed to strengthening your security posture together, moving far beyond a simple report to deliver real, lasting results.

Our approach is built on clarity, collaboration, and tangible outcomes. We know that business leaders want more than a dense, technical document; they want the peace of mind that comes from knowing their defences are solid and their data is safe. That is why we have developed a comprehensive 10-step engagement process designed to be thorough and transparent, all while causing minimal disruption to your daily operations.
Many providers will find your vulnerabilities, hand you a detailed report, and consider the job done. This approach often leaves internal IT teams overwhelmed, struggling to interpret findings and prioritize fixes on top of their existing responsibilities. This model is inefficient. A report gathering dust on a shelf does nothing to make you safer.
This is where our Managed Remediation truly sets us apart.
We do not just find the problems; we roll up our sleeves and work with your team to fix them. Our experts provide clear, step-by-step guidance, help implement the necessary changes, and then verify that the fixes actually work. This hands-on approach ensures critical vulnerabilities get closed—fast.
This is a core part of our philosophy. Your team gains valuable insights from our specialists, building their own skills while we actively reduce your attack surface. It is what turns a standard test into a genuine security partnership. You can see how this proactive support fits into a wider strategy in our guide to managed security services.
Consider a recent engagement with a mid-sized Canadian logistics company. Their customer portal, which handled sensitive shipping data, was the heart of their business. Our penetration test uncovered a chain of complex vulnerabilities that, if exploited, could have allowed an attacker to access client information and halt their supply chain.
Instead of just handing over a report, we scheduled working sessions with their developers. We walked them through the entire attack chain, explained the root causes, and provided concrete, code-level recommendations. Supported by our 24/7 Canadian Helpdesk, we answered their questions in real-time as they implemented the fixes. A follow-up retest confirmed every vulnerability was successfully closed.
The result was not just a secure portal but also a more knowledgeable client team and a stronger, more resilient security posture for the long term.
The need for this deeper level of security is growing across every sector. In 2023, large enterprises and the BFSI (Banking, Financial Services, and Insurance) sector were major drivers in the North American penetration testing market. This is understandable—they have vast IT infrastructures and sensitive financial data that are prime targets for cyber threats. You can read more on industry trends in this comprehensive market analysis.
Our hands-on approach delivers the expert support that medium-sized businesses in critical Canadian industries need to face these challenges. We provide the expertise and the follow-through to ensure your investment in penetration testing translates directly into a safer, more secure business.
Exploring penetration testing for the first time naturally brings up questions. As a business leader, you need clear answers to make an informed decision, especially regarding value, frequency, and potential impact on your daily operations. Let us address some of the most common concerns we hear.
One of the first questions people ask is about the difference between a vulnerability scan and a full penetration test. An automated vulnerability scan is like a quick security checklist; it is effective at finding low-hanging fruit like known software bugs or missing patches. It is a useful tool, but it has its limits.
A penetration test, however, is driven by the creativity and expertise of a human ethical hacker. They do not just find a vulnerability on a list. They think like a real attacker, chaining together seemingly minor flaws to see how far they can get and demonstrating the actual business impact of a breach. That human element is what uncovers the complex risks that automated tools will always miss.
There is no single answer that fits every business, but a solid baseline is to schedule a test at least once per year. However, certain events should trigger a test more often.
You should book a test if you:
Regular testing ensures your security keeps pace with your business as it evolves. To get a better sense of the strategic advantages, you can learn more about the five key business benefits of penetration testing in our detailed guide.
Think of penetration testing like a regular health check-up for your digital infrastructure. An annual test provides a consistent baseline, while event-driven tests address specific changes, ensuring new risks are identified and managed before they become critical problems.
This is a valid concern. The idea of a simulated attack might sound disruptive, but a professional engagement is the opposite. The most important part of any test happens before any "hacking" begins: the scoping and planning phase.
During this stage, we work closely with your team to set crystal-clear "rules of engagement." We define precisely which systems are in scope, what techniques are allowed, and schedule testing windows during off-peak hours to ensure zero impact on your daily work. The entire process is carefully controlled, completely transparent, and supported by open communication. A professional penetration test is designed to find your weaknesses safely, not create new ones.
At CloudOrbis Inc., we believe a penetration test is the start of a security partnership. We provide the clarity and expertise you need to turn findings into real security improvements. Protect your business with confidence by exploring our security solutions.
Learn more at https://cloudorbis.com.
June 5, 2026
Serverless Architecture for Canadian SMBs: Guide 2026Practical guide to serverless architecture for Canadian SMBs. Learn benefits, costs, security, & migration tips. Migrate with confidence in 2026.
Read Full Post
June 4, 2026
IT Asset Management: A Guide for Canadian SMBsLearn how effective IT asset management can boost security, control costs, and drive growth for your Canadian SMB. A practical guide to getting started.
Read Full Post
June 3, 2026
Maximize Efficiency: Workflow Automation Tools 2026Boost efficiency & ROI for Canadian SMBs with workflow automation tools. Explore benefits, use cases, and our implementation roadmap.
Read Full Post