May 29, 2026
Your Guide to Business Process Optimization in CanadaUnlock efficiency with our guide to business process optimization. Learn a step-by-step framework for Canadian SMBs, from process mapping to technology and ROI.
Read Full Post%20(1).webp)
Usman Malik
Chief Executive Officer
February 28, 2026
For any business in Alberta, the question is no longer if a cyberattack will happen, but when. Managed cybersecurity offers a proactive defence, letting you partner with experts to shield your operations, data, and hard-earned reputation. It’s a strategic shift from reacting to threats toward building a resilient security posture designed for Alberta's unique economic landscape.
The idea that cybercriminals only go after massive, multinational corporations is a dangerous myth. The reality is that small and medium-sized businesses (SMBs) right here in Alberta are increasingly in their crosshairs. Your valuable data, your connections to larger supply chains, and often, your limited security resources make you an attractive and surprisingly lucrative target.
A reactive, "break-fix" approach to security simply doesn't cut it anymore. Waiting for a breach to happen before you act is like waiting for your office to catch fire before buying an extinguisher. By then, the financial and reputational damage can be irreversible, grinding your operations to a halt and shattering the trust you've built with your customers.
Recent data drives home the urgency for a stronger defence. In 2023, Alberta saw a staggering 24% surge in reported cybercrimes, totalling 12,124 separate incidents. This spike is especially concerning for SMBs in our major hubs like Calgary and Edmonton.
A report from CyberAlberta also shows that identity theft jumped by 11%, while fraud and various scams impacted 50% of businesses. You can dig into the full findings in their CyberAlberta Threat Intelligence update.
This screenshot from CyberAlberta's homepage highlights the province-wide focus on strengthening our digital defences.
The site acts as a central hub, showing a coordinated effort between government and industry to share threat intelligence and promote better security practices. For your business, this means that while awareness and tools are growing, so are the stakes.
The biggest takeaway here is that threats aren't just growing in number—they're becoming more sophisticated. Ransomware attacks, for instance, more than doubled in 2024. This proves that attackers are becoming more aggressive and, unfortunately, more successful in their campaigns against Albertan organizations.
Certain sectors that form the backbone of Alberta's economy face distinct risks. These are just a few examples of the top cybersecurity threats SMBs face today.
Ultimately, investing in a robust managed cybersecurity Alberta plan isn't just another IT expense; it's a fundamental business strategy for survival and growth. It lets you trade constant worry for the confidence to focus on what you do best—running your business.
When you sign on with a managed cybersecurity provider, you're not just buying a piece of software. You're bringing a dedicated team of security experts into your corner. But what does that partnership look like day-to-day? Knowing the core components helps you see how that investment directly translates into a stronger, more resilient business.
Think of it like securing your physical office. You wouldn't just put one lock on the front door and call it a day. You'd have guards, alarm systems, reinforced windows, and a clear plan for what to do if someone tries to break in. Managed cybersecurity works the same way by creating layers of defence for your digital world.
This flowchart shows just how quickly cyber threats can escalate and what that means for Alberta's small and mid-sized businesses.
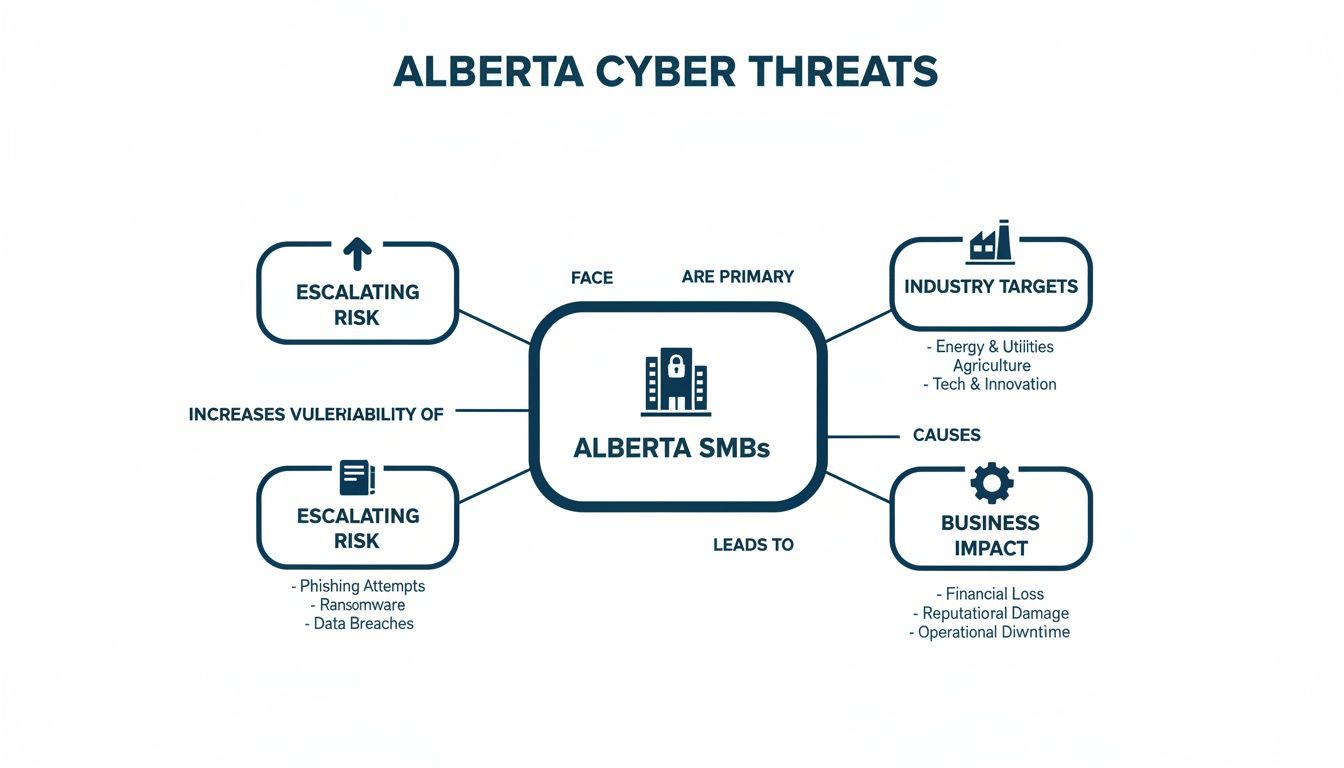
As you can see, the risks are very real, with specific industries targeted. A single incident can cause a ripple effect, disrupting operations across our province's key sectors.
Imagine having a digital security team that never sleeps, eats, or takes a holiday. That's 24/7 monitoring in a nutshell. This service is all about constant surveillance of your networks, servers, and devices, watching for any sign of trouble.
This isn't just about catching known viruses. It's about using sophisticated threat detection tools to spot unusual patterns that could signal a new or hidden threat. The moment an anomaly is found, an alert goes to a team of security analysts who investigate immediately. This round-the-clock watch is critical, especially since attacks often happen after everyone has gone home for the day.
What is an "endpoint"? It's any device connected to your business network—laptops, desktops, servers, and even mobile phones. Every single one is a potential way in for an attacker. Endpoint protection is about ensuring every digital door and window to your business is locked down tight.
This goes far beyond your standard antivirus software. A managed provider uses advanced tools that can:
By centrally managing and securing every device, your partner drastically shrinks your company's attack surface.
A great security partner doesn't just sit back and wait for threats. They actively hunt for weaknesses. Vulnerability management is the process of regularly scanning your systems for known security holes, outdated software, or misconfigurations that an attacker could exploit.
Once found, these vulnerabilities are prioritized and patched. It’s like fixing a broken lock before a burglar finds it.
To get the full picture, providers use Security Information and Event Management (SIEM) technology. A SIEM system is the central command hub, pulling in and analyzing security data from your entire IT environment. It connects the dots between alerts from different sources—like firewalls, servers, and endpoints—to spot complex threats that might otherwise fly under the radar. When you're looking at your options, understanding the vital functions of a firewall helps show how these different services work together to protect you.
Key Takeaway: A SIEM gives security experts the context they need to distinguish a real threat from a false alarm. It turns a flood of raw data into actionable intelligence, allowing for a much faster and more accurate response.
Even with the best defences in place, a security incident can still happen. What you do next is what truly matters. An incident response (IR) plan is your playbook for handling a breach. It’s a pre-defined, step-by-step strategy that ensures a swift, coordinated, and effective response to contain the damage and get back to business.
Your managed cybersecurity partner will work with you to build and test this plan. If an incident does happen, their team leads the response, handling everything from technical containment to preserving evidence. Having that expert guidance during a high-stress crisis is invaluable, helping your business recover faster and with far less fallout. If you want to dive deeper into what makes up a full security program, check out our guide on what to expect from MSSP security services.
For any business in Alberta, compliance isn't just about checking a box; it’s the bedrock of trust and operational integrity. Falling short on provincial and federal data protection rules can bring serious financial penalties and do lasting damage to your reputation. This is where partnering with a managed cybersecurity in Alberta expert becomes a game-changer, turning complex legal obligations into a clear, manageable process.
The compliance world is always shifting, thanks to new regulations and evolving government strategies. For instance, Alberta's 2024 Cybersecurity Strategy is changing how businesses see security by encouraging public-private information sharing and stressing the need to prepare for quantum computing. This push for shared threat intelligence and stronger security is part of a bigger picture, as Canada's cybersecurity spending is expected to jump from USD 9.67 billion in 2026 to USD 18.26 billion by 2031.
At the heart of Alberta's privacy rules are two major laws: the provincial Personal Information Protection Act (PIPA) and the federal Personal Information Protection and Electronic Documents Act (PIPEDA). While they sound similar, they serve different functions. PIPA dictates how private companies inside Alberta can collect, use, and share personal information.
PIPEDA, on the other hand, covers federally regulated industries (like banking and telecommunications) and any data that crosses provincial or international borders. Depending on your business operations, you could be accountable under both.
A managed cybersecurity partner helps you make sense of this tricky terrain by implementing crucial controls. This isn't just theory; it means practical, hands-on protection.
For many businesses, the first step is a formal review of how data is handled. You can learn more about this process in our guide to running a Privacy Impact Assessment in Alberta.
On top of these foundational laws, many Alberta industries face their own unique set of compliance challenges. This is especially true for the sectors that drive our provincial economy.
An Edmonton-based medical clinic, for example, must follow strict rules under PIPA for handling patient health information. A single breach could lead to massive fines and completely destroy patient trust. A managed security partner provides the specific controls they need, like securing electronic health records (EHR) and ensuring all communications are encrypted.
In the energy sector, the pressure is even more intense. The Security Management for Critical Infrastructure Regulation forces certain facilities designated by the Alberta Energy Regulator to build a complete security program. This includes tough cybersecurity measures to shield both information technology (IT) and operational technology (OT) systems from attack.
And while you're focused on Alberta's rules, it’s also crucial for any business that processes credit cards to work through a detailed PCI DSS compliance checklist.
A managed provider helps these organizations meet their obligations by delivering around-the-clock monitoring, vulnerability management, and the detailed reporting needed to prove due diligence to regulators. This turns compliance from a frustrating cost into a real business advantage.
Deciding on a managed cybersecurity model isn't just about picking a service; it's a strategic choice that will shape your IT and security for years to come. Think of it like a home renovation. Are you hiring a general contractor to handle the entire project from start to finish (fully managed)? Or are you acting as the project lead yourself, bringing in expert tradespeople for specific jobs like electrical and plumbing (co-managed)?
Neither approach is automatically better. The right fit hinges entirely on your company’s goals, in-house resources, and budget. This decision defines the relationship you'll have with your security partner and clarifies who is responsible for what. Getting it right from the start ensures you get the precise support you need without overpaying for services you don't.
The co-managed model is all about partnership. It’s built for businesses that already have an IT team but need to enhance their skills, plug specific expertise gaps, or simply free up their people to focus on big-picture projects instead of being buried in daily security alerts. Your team and your provider work hand-in-hand, often sharing tools and splitting responsibilities.
Imagine a growing manufacturing company in Red Deer. Their small IT team is fantastic at keeping the production line's tech running smoothly, but they might not have the specialized knowledge or advanced tools for 24/7 threat hunting.
Under a co-managed agreement, a provider could take over those specialized duties. This gives the internal team access to enterprise-grade security tools and expert backup, supercharging their capabilities without the hefty expense of hiring multiple new security analysts. If this collaborative approach sounds right for you, we explore it further in our article on co-managed IT services in Edmonton.
A co-managed partnership doesn't replace your IT team—it empowers them. It gives them the advanced tools and expert backup they need to defend the business, all while they maintain control and continue to drive internal strategy.
In contrast, a fully managed model is a complete, hands-off solution. Here, you're outsourcing your entire cybersecurity function to a dedicated provider. They essentially become your security department, taking ownership of everything from strategy and implementation to monitoring, incident response, and reporting.
This model is a perfect fit for organizations with little or no internal IT staff, or where the current team is already stretched too thin. Take a busy Calgary law firm, for instance. Their expertise lies in the law, not in firewalls and endpoint protection, yet they handle incredibly sensitive client data that falls under strict PIPA regulations.
For this firm, a fully managed solution offers total peace of mind. The provider assumes full responsibility for their security posture, ensuring compliance, protecting data, and handling any incidents that arise. This allows the partners and staff to focus exclusively on serving their clients, confident that their digital operations are in expert hands. Choosing a provider that offers managed cybersecurity in Alberta also guarantees they bring local expertise on provincial privacy laws to the table.
To help you weigh your options, here’s a quick comparison of the two models:
Ultimately, choosing between these models is a pivotal first step. Take a hard look at your team's skills, your available budget, and how much day-to-day control you want to retain. A co-managed approach offers a powerful mix of internal know-how and external expertise, while a fully managed model delivers complete security ownership and priceless peace of mind.
Choosing a provider for managed cybersecurity in Alberta is one of the most critical decisions you'll make for your company. The right partner becomes a true extension of your team, a trusted advisor laser-focused on your long-term success. The wrong one can be a costly mistake, leaving you with a false sense of security and a transactional relationship that delivers little real-world value.
To see past the sales pitch and find a genuine partner, you have to ask the right questions. It’s not just about a list of services they offer, but how they deliver them, what experience they bring to the table, and how their strategy aligns with your actual business goals. A great partner cuts through the technical jargon and connects their work directly to your operational stability and growth.
When you sit down with potential providers, your goal is to get to the heart of their capabilities, operational model, and local expertise. Don't be shy about digging deep with specific, probing questions that reveal the substance behind their marketing claims.
Here are the essential questions you should ask every candidate:
Expert Insight: A true partnership is built on shared outcomes, not just service-level agreements. The best providers work to understand your business objectives and tailor their security strategy to help you achieve them, turning cybersecurity from a cost centre into a business enabler.
Beyond their technical expertise, you need to feel out how a provider operates and what it would actually be like to work with them day-to-day. A transactional vendor simply sells you a package of services. A strategic partner, on the other hand, invests in your success. They are proactive, communicative, and transparent.
Look for these signs that point toward strong partnership potential:
Finding an effective provider is about much more than their tech stack; it’s about finding an organization whose values and approach align with yours. Taking the time to thoroughly vet your options now will pay off tenfold with a resilient, secure business ready for whatever comes next. For more on selecting the right fit, explore our guide on finding the best managed service provider in Alberta.
Thinking about overhauling your company’s security can feel like a massive project. But it doesn't have to be a painful, all-at-once disruption. With the right partner, it's a structured journey that systematically strengthens your defences without getting in the way of business. Think of it as a clear roadmap, designed to take your organization from a state of constant worry to one of confident growth.
It’s like building a custom security framework piece by piece, ensuring each layer is solid before moving on to the next. This methodical approach is the key to a smooth and truly effective implementation.
You can't get to where you're going without knowing where you are right now. The first step is always a thorough risk assessment—a diagnostic for your business's digital health. Your new partner will dive deep into your existing IT environment to find potential vulnerabilities, misconfigurations, and compliance gaps specific to your Alberta operations.
This isn't just a technical scan; it's a business-focused analysis. The goal is to pinpoint the biggest risks to your data, daily operations, and reputation. This phase gives you a crystal-clear picture of your security posture before a single change is made.
With a clear map of your risks, the next move is to build a strategy that works for you. This is where your partner designs a security architecture that directly plugs the holes found during the assessment. They'll help prioritize what to tackle first based on risk level and business impact, creating a logical, step-by-step plan.
This stage involves:
This collaborative planning ensures the final solution is perfectly aligned with both your business goals and your budget.
A well-designed security roadmap isn’t just about technology; it’s about process and people. It ensures every aspect of your business is considered, creating a truly holistic defence that integrates seamlessly into your daily operations.
With the blueprint in hand, it’s time to start building. Instead of a chaotic "rip and replace" approach, new technology is deployed in carefully managed phases. This might mean starting with foundational protections like endpoint security and multi-factor authentication (MFA) before moving on to more advanced solutions like a SIEM system.
Each stage is meticulously tested and validated to ensure it works flawlessly within your existing setup. This methodical rollout gives your team time to adapt to new tools and processes, which dramatically reduces friction and leads to much smoother adoption across the company.
Technology alone is never the complete answer. Your team is your first and most critical line of defence. The final, ongoing phase focuses on empowering your employees with the knowledge they need to spot and sidestep threats. A good partner provides security awareness training that’s engaging and relevant to their jobs.
This means teaching staff how to identify phishing emails, use strong passwords, and handle sensitive data securely. By building a security-conscious culture, you turn what could be your biggest vulnerability into your greatest security asset. This final step is what makes your resilient posture stick long after the initial setup is complete.
Making the leap to managed cybersecurity is a big decision, and you will naturally have questions. To help clarify, we’ve put together answers to the most common questions we hear from business leaders like you across Alberta.
This is always the first question, and the honest answer is: it depends. The cost of managed cybersecurity in Alberta isn't a one-size-fits-all number. It hinges on factors like your company's size, the complexity of your IT setup, and the exact services you need. A business with 20 employees will have a very different price point than a larger operation with multiple sites and strict compliance demands.
Most providers use a tiered pricing model, usually a predictable monthly subscription per user or per device. This approach eliminates surprise bills and allows you to treat security as a fixed, budget-friendly operational expense. The goal is to find a plan that gives you the right level of protection without making you pay for features you don’t actually need.
Absolutely. In fact, that's exactly what a co-managed IT model is for. A managed security provider is there to amplify your existing IT team, not replace them.
Think of it this way: by partnering with a provider, you’re giving your in-house team a direct line to advanced security tools and a squad of specialized experts for 24/7 monitoring and incident response. This frees them from the constant grind of security alerts so they can focus on strategic projects that grow your business.
The timeline for getting everything up and running really depends on the scope of services. A reputable provider won't just flip a switch; they'll use a structured, phased approach to ensure there's minimal disruption to your daily operations.
The initial process usually looks like this:
A good partner will give you a clear timeline and keep you in the loop every step of the way, ensuring the transition is as smooth as possible. The aim is to get your core defences in place quickly while methodically building out a more mature security program over time.
Choosing a provider with deep roots in Alberta gives you a home-field advantage. A local partner truly understands our specific regulatory landscape, including the ins and outs of Alberta’s Personal Information Protection Act (PIPA). They also have first-hand experience with the unique threats facing our province’s key industries, from the energy sector to healthcare.
This local expertise means your security strategy isn’t just a generic template—it’s built to be effective and fully compliant with the laws that govern your business right here in Alberta.
Ready to trade constant worry for the confidence that comes with expert protection? The team at CloudOrbis Inc. delivers proactive, 24/7 managed cybersecurity tailored to the unique needs of Alberta businesses. Secure your business and book a consultation today.
May 29, 2026
Your Guide to Business Process Optimization in CanadaUnlock efficiency with our guide to business process optimization. Learn a step-by-step framework for Canadian SMBs, from process mapping to technology and ROI.
Read Full Post
May 28, 2026
Manage iPhone Application Permissions for Business SecurityMaster iPhone application permissions to secure your business data. Guide covers access management, enterprise controls & compliance for Canadian SMBs.
Read Full Post
May 27, 2026
Threat Detection and Response: A Guide for Canadian SMBsLearn to build an effective threat detection and response strategy. Our guide for Canadian SMBs covers key tools, implementation roadmaps, and compliance.
Read Full Post