
June 8, 2026
What Is IT Vendor Management? a Guide for Canadian SMBsLearn what is IT vendor management, its lifecycle, benefits, and risks. Our guide for Canadian SMBs covers best practices for security and compliance.
Read Full Post%20(1).webp)
Usman Malik
Chief Executive Officer
March 10, 2026
What exactly is managed IT services security? Think of it less like a product and more like a strategic partnership. It’s where an expert third-party provider, like CloudOrbis, takes complete ownership of designing, managing, and defending your entire digital environment. This proactive approach gives your business access to top-tier security tools and a dedicated team of specialists, all for a predictable monthly cost.

Picture your business as a digital fortress. Inside, you hold your most valuable assets—client data, financial records, and proprietary information. Every day, that fortress is under siege from sophisticated cybercriminals. Without a team of architects, engineers, and 24/7 guards, its walls are dangerously exposed. This is precisely the role that managed IT services security fills.
A managed security service provider (MSSP) becomes your expert defence force. Instead of you having to find, train, and equip an in-house security team, you gain a partner who assumes full responsibility for your cybersecurity posture. This single move solves several critical challenges that many Canadian businesses grapple with.
For most medium-sized organizations, building a truly robust internal security department is not realistic. The obstacles are clear:
By outsourcing your security, you are not just offloading tasks; you are adopting a proactive strategy that integrates high-level expertise and technology directly into your operations. This allows you to focus on growth, confident that your digital assets are protected around the clock.
Before we dive deeper into the specifics, it’s helpful to have a solid understanding of what network security is and its core principles. A firm grasp of this concept clarifies why a comprehensive managed approach is so effective. This guide will walk you through everything you need to know about building a resilient security strategy that protects your assets and empowers your business. If you are also interested in the broader scope, you might be interested in our article on the fundamentals of a managed IT service.

An effective managed IT security strategy is not a single piece of software you install and forget. It is a complete system of interconnected defences that work together. Each layer tackles a different type of risk, forming a resilient shield around your entire business. It is vital to think of your security in layers; if one defence is bypassed by an attacker, another is already in place to stop them.
Think of it like a medieval fortress. You would not just rely on a tall wall. You would have watchtowers, a moat, reinforced gates, and guards patrolling inside. Each element has its own job, but they all work in concert. This integration is what turns a random collection of security tools into a unified strategy that actively defends your organization.
Let's break down the pillars that make up this modern defensive system.
Imagine having a dedicated security team watching over your digital operations every second of the day, even while you sleep. That is the core of 24/7 threat monitoring and response. Using a mix of advanced technology and human expertise, this service constantly analyzes activity across your network, servers, and employee devices.
When something suspicious happens—like strange login attempts from an unusual location or unexpected data movement—an alert is triggered instantly. Your managed security team investigates immediately to determine what is happening and neutralizes the threat before it can turn into a devastating breach. This constant vigilance is non-negotiable, as attackers often strike outside of normal business hours. To see how this active threat hunting works, you can learn more about managed detection and response.
Every device connected to your company network is an endpoint. This includes laptops, desktops, servers, and even mobile phones. Each one is a potential doorway for an attacker. Today's endpoint security is leagues beyond the simple antivirus software of the past.
Think of it as giving each device its own suit of intelligent, responsive armour. This protection is built to spot and block sophisticated attacks like ransomware, zero-day malware, and phishing attempts as they happen. It ensures that even if an employee accidentally clicks on a malicious link, the device is fortified to contain and eliminate the threat before it can infect the rest of your network.
A managed security provider takes the guesswork out of device security. They ensure every endpoint is consistently updated, patched, and monitored from a central point, closing security gaps that emerge when maintenance is left to individual users.
Even the strongest fortress wall can develop cracks over time. In the digital world, these cracks are software vulnerabilities—flaws in the code of your applications and operating systems that hackers can exploit. Vulnerability management is the process of proactively hunting for these weaknesses across your entire IT environment.
This is not a one-time scan; it is a continuous cycle:
A prime example was the critical vulnerability found in GoAnywhere MFT (CVE-2025-10035), which could have allowed attackers to run their own code on a company’s server. A managed security team would have immediately identified which clients were at risk and applied the patch, shutting the door on that threat.
What if the worst still happens? Despite having multiple layers of defence, a catastrophic event—a fire, a flood, or a brand-new ransomware variant—is always a possibility. This is where your data backup and disaster recovery (BDR) plan becomes your ultimate safety net.
Think of BDR as having a secure, off-site vault with perfect copies of your most critical data, applications, and system configurations. If a disaster strikes, your BDR plan is the playbook that allows you to restore your operations quickly, ensuring you get back to business with minimal downtime and data loss. Building a solid plan starts with understanding the basics, and reviewing expert cybersecurity tips for small businesses is a great place to start.
For many Canadian businesses, following industry and government regulations is not just good practice—it is the law. Compliance management is the component that ensures your security posture meets the strict standards set by laws like the Personal Information Protection and Electronic Documents Act (PIPEDA).
A managed provider with deep expertise in Canadian compliance frameworks will configure your systems and implement the necessary policies to safeguard sensitive data. This helps you avoid the risk of steep fines, legal trouble, and the reputational damage that comes with a compliance failure.
Understanding the difference between traditional IT help and modern managed security is crucial. Traditional support is reactive—you call when something breaks. A managed security service, on the other hand, is proactive, designed to prevent things from breaking in the first place.
Here is a clear breakdown of the two approaches:
Ultimately, while traditional IT might solve a computer problem, a managed security service protects the entire business from the countless digital threats that exist today. It is a strategic partnership focused on keeping your organization safe, compliant, and running smoothly.
Partnering with a managed security provider is much more than a technology upgrade; it is a strategic business move. For leaders, the real value is not just in firewalls and software—it is measured in stability, efficiency, and uninterrupted growth. A proper security partnership translates complex technical safeguards into tangible advantages that strengthen your entire organization.
When you shift from a reactive, break-fix IT model to a proactive security partnership, you fundamentally change how your business operates. Resources move away from constant firefighting and toward activities that drive revenue. Instead of cleaning up after a security incident, you can confidently focus on innovation, customer care, and strategic growth.
One of the biggest wins for any business leader is swapping unpredictable IT expenses for a fixed, manageable monthly cost. Without a dedicated security plan, a single cyberattack can trigger massive, unplanned costs for remediation, data recovery, and potential fines. That kind of financial volatility makes budgeting a nightmare.
A managed security partnership bundles all the necessary tools, expertise, and 24/7 monitoring into a single, predictable subscription. This model eliminates surprise bills and is far more cost-effective than trying to build an equivalent security team in-house.
Think about it: when you weigh the average salary of just one senior cybersecurity expert in Canada against a full team of specialists from a provider, the return on investment is clear. You get enterprise-grade protection without the overhead of salaries, benefits, training, and costly software licences.
The cybersecurity skills gap is a real and pressing challenge for businesses across Canada. Finding, hiring, and retaining top-tier security talent is both incredibly difficult and expensive. A partnership with a managed security provider instantly solves this problem by giving you access to an entire team of certified professionals.
This team is made up of specialists in different, crucial domains:
This collective expertise ensures your business is defended by specialists at the top of their game—a level of protection most medium-sized businesses could not achieve on their own. Our guide on the broader benefits of managed IT services explores this advantage in more detail.
How much time does your team currently lose to IT distractions, security alerts, and routine maintenance? Every hour spent on those tasks is an hour not spent on core objectives like developing new products, closing sales, or serving your customers. A security partnership lifts that burden from your team's shoulders.
With experts handling your security, your employees can finally concentrate on what they do best. This clear separation of duties boosts productivity and lets you point your internal resources toward strategic initiatives that directly contribute to the bottom line. Your IT transforms from a source of constant interruption into a true enabler of progress.
In Canada, failing to comply with data privacy laws like PIPEDA can lead to crippling financial penalties and cause irreparable damage to your brand. A managed security provider with deep expertise in Canadian compliance ensures your systems and processes meet every necessary standard.
This not only keeps you out of legal hot water but, just as importantly, it builds trust with your clients. When customers know their sensitive information is secure, it strengthens your reputation and gives you a significant competitive edge. With a 100% Canada-based 24/7 helpdesk, you also gain the assurance that your data is managed entirely under Canadian jurisdiction, further reducing risk and guaranteeing data sovereignty.
Cybersecurity is never a one-size-fits-all game. A manufacturing plant has entirely different risks than a law firm, and a healthcare clinic faces compliance rules that a construction company never will. Real managed it services security comes from a partner who understands the unique pressures and regulatory landscape of your specific industry.
Without that industry-specific focus, a generic security plan is full of holes waiting to be exploited. A partner with deep sector knowledge tailors your defences to the threats that matter to your business. This turns your security from a simple cost centre into a genuine strategic asset.
For any Canadian healthcare organization, whether it is a local clinic or a hospital network, the mission is clear: protect electronic personal health information (ePHI). Provincial privacy laws, like Ontario's PHIPA, have strict rules for how this sensitive data is stored, sent, and accessed. A single breach is not just a public relations nightmare; it carries heavy legal and financial penalties.
An expert security partner knows how to meet these non-negotiable demands with specific controls:
In the world of manufacturing and logistics, uptime is everything. An attack that freezes a production line or scrambles a supply chain causes immediate and devastating financial damage. The biggest risk today comes from the merger of Information Technology (IT) with Operational Technology (OT)—the systems controlling the physical machinery on the floor.
Protecting this combined IT/OT environment is a unique puzzle. Your security plan must cover the office network and the Industrial IoT sensors, robotics, and control systems on the factory floor. The goal is to safeguard your supply chain integrity by locking down these often-overlooked digital entry points.
For manufacturers, a cyberattack is not just a data problem; it is a physical one. A security provider must understand how to protect OT systems without disrupting the sensitive, real-time processes they manage, ensuring both digital and physical operations remain secure.
For law firms and financial institutions, business is built on a foundation of trust. The data you manage, from confidential case files to personal financial records, is extremely valuable and tightly regulated. Adhering to national regulations like the Personal Information Protection and Electronic Documents Act (PIPEDA) is not optional.
A security partner working in these fields must focus on several key areas:
This is why it is so vital to find a provider who speaks your industry's language. When you are assessing your options, ask them about their experience in your sector. To see the kinds of specialized security solutions we build, you can learn more about our work across different Canadian industries.
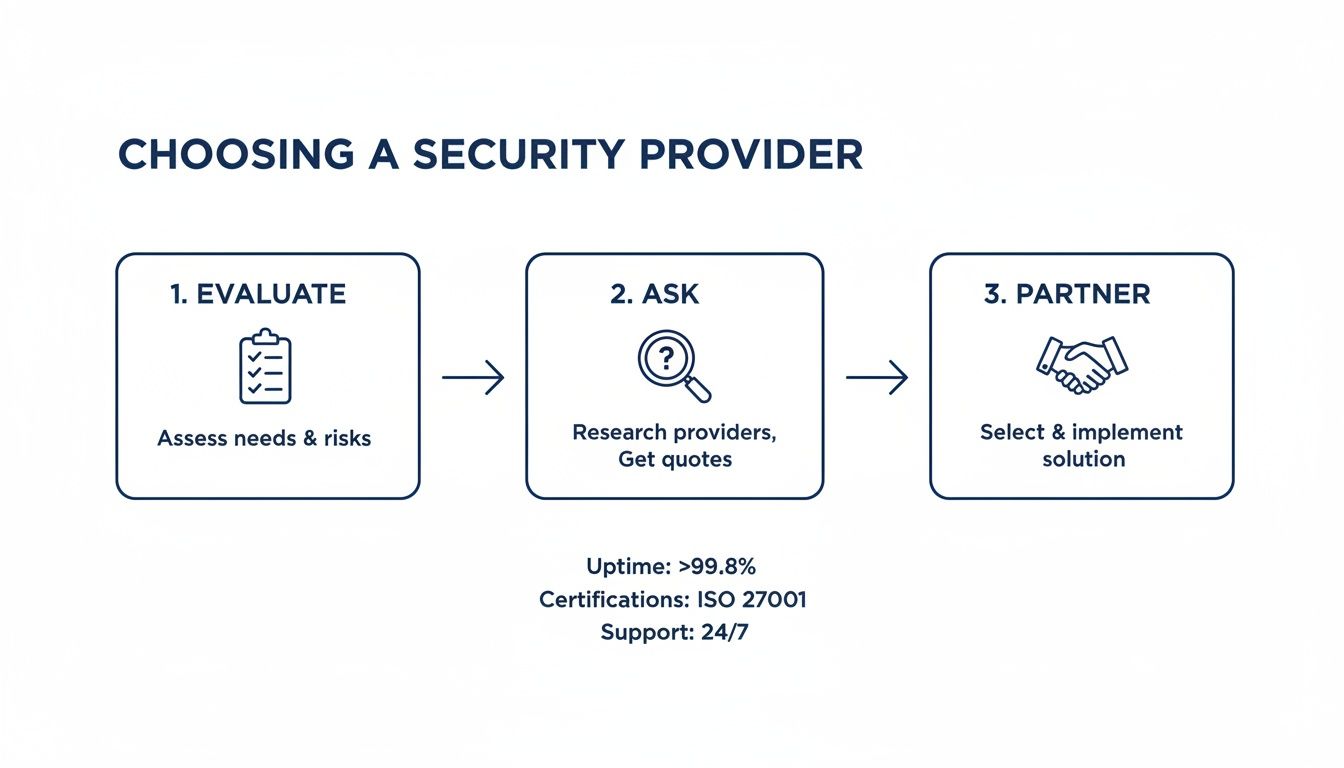
Choosing a partner to handle your business's security is one of the most important decisions you will make. This choice is about more than just technical specifications; it is about finding a true partner who is genuinely committed to your long-term resilience and success. The right provider acts as a natural extension of your team, while the wrong one can leave you with glaring security gaps and compliance headaches.
While the selection process might feel overwhelming, breaking it down into a structured approach can turn it into a confident, well-informed decision. You are not just looking for a vendor to sell you software. You are trying to find a strategic ally who understands your business, foresees risks, and has a proven history of proactive defence.
To differentiate real partners from mere vendors, you need to ask the right questions. Their answers will reveal everything about their capabilities, their operational processes, and whether they are truly invested in your success. A provider who answers these questions with confidence and transparency is one worth your time.
Here is a practical checklist of questions you should ask any potential managed security provider:
Is your Security Operations Centre (SOC) located and staffed entirely within Canada? For data sovereignty, this is non-negotiable. A Canada-based SOC guarantees your sensitive data remains within our borders, governed by Canadian privacy laws like PIPEDA, and is supported by a team that understands the local business environment.
What are your guaranteed Service Level Agreements (SLAs) for threat response and issue resolution? Vague promises are not enough. Ask for specific, contractually guaranteed response times. For example, how quickly will they acknowledge a critical alert, and what is the guaranteed time to resolution?
Can you provide case studies or references from our specific industry? A provider with proven experience in your sector—whether it is healthcare, manufacturing, or finance—will already be familiar with your unique compliance needs and the specific threats you face.
How do you support a proactive security mindset beyond just monitoring alerts? Look for proof of strategic guidance. Do they perform regular vulnerability scans, hold strategic business review meetings, and provide comprehensive security awareness training for your staff?
By asking these direct questions, you can cut through the marketing noise and get a clear sense of what a partnership would actually feel like day-to-day.
A true security partner does not just react to alerts; they actively work to reduce your attack surface. They should feel like a strategic advisor who is consistently bringing new ideas to the table to strengthen your defences and improve your overall security posture.
A reactive provider waits for something to go wrong. A proactive partner works tirelessly to prevent things from going wrong in the first place. This proactive mindset is the single most important quality to look for. It is the difference between having a simple monitoring service and having a comprehensive managed IT services security strategy.
Look for tangible evidence of this proactive approach:
To make your decision process even clearer, use this simple scorecard to compare potential providers side-by-side. Rate each provider on a scale of 1 (poor) to 5 (excellent) based on the criteria that matter most for a long-term, successful partnership.
This scorecard helps you move beyond a gut feeling and make an objective, data-driven decision. The provider with the highest score is likely the one best aligned with your security needs and business goals. Choosing the right provider is a foundational step in securing your business's future. For a deeper look into the different types of providers, check out our guide on what to expect from MSSP security services.
Making the switch to managed IT services security can feel like a huge leap, but it does not have to be a disruptive one. The journey to better protection should not be complicated or chaotic. At CloudOrbis, we have built our entire approach around a transparent, 10-step engagement process that delivers value right from day one.
Think of it as a well-managed project, not an overwhelming overhaul. We start with a no-obligation security assessment to get a clear picture of your environment, risks, and goals. From there, we guide you through strategic planning, smooth onboarding, and practical employee training, making sure every step is handled with minimal interruption to your business.
Our model is not just about providing tools; it is about providing guidance. You are assigned a dedicated Virtual CIO (vCIO) who serves as your high-level strategic advisor, working with you to ensure your technology roadmap perfectly aligns with your business ambitions. This ensures your security does not just meet today's needs but evolves as you grow.
This long-term strategy is balanced with immediate, on-the-ground support. Our unique 'one-click IT Button' gives your team instant access to our 100% Canada-based helpdesk. Expert help is literally just a single click away.
A partnership with CloudOrbis is built on a proven process that makes upgrading your security straightforward and predictable. The goal is to deliver both immediate peace of mind and long-term value, turning your IT from a liability into a strategic asset.
Our 10-step process takes the mystery out of achieving robust security. We manage every detail, from the initial deep-dive assessment and custom strategy creation to implementing the right defences and providing constant, proactive oversight. It is a complete lifecycle approach built for lasting resilience.
The journey with us includes critical milestones like:
This structured engagement ensures you do not just get the right security tools, but also the expert processes needed to make them truly effective.
Your path to a more secure and efficient business can begin today. Book a simple, no-obligation consultation to take the first step. Let's talk about your challenges and show you how a clear, proven process can make all the difference.
When it comes to managed IT services security, business leaders often have a few practical questions. Let's tackle some of the most common ones to give you a clearer picture as you consider a security partnership.
There is no single price tag for security. The cost is usually a predictable monthly subscription based on factors like the number of people on your team, the complexity of your IT setup, and which specific services you need. This model eliminates the surprise costs that often follow a security incident.
When you weigh this investment against the astronomical cost of a data breach—which includes downtime, regulatory fines, and damage to your reputation—the return on investment becomes crystal clear. It is almost always more cost-effective than trying to build and retain an equivalent security team in-house.
Absolutely. This setup is known as a co-managed IT model, and it is a scenario where we excel. We do not come in to replace your existing staff; we are there to make them more effective.
Your internal IT person knows your business inside and out, so they can focus on strategic projects that drive growth. We handle the intensive, specialized work of 24/7 threat monitoring, complex incident response, and continuous vulnerability management. Together, we create a powerful, collaborative team.
The exact timeline for onboarding depends on the size and complexity of your organization, but it is always a structured process with clear communication. Our goal is to make the transition smooth and seamless, with as little disruption to your daily operations as possible. We manage everything from the first assessment to the final deployment, keeping you in the loop every step of the way.
Choosing a provider based right here in Canada is crucial for a few key reasons:
Ready to secure your business with a proactive, Canada-based partner? Contact CloudOrbis to start your journey toward a more resilient and efficient future. Book your no-obligation consultation at https://cloudorbis.com.

June 8, 2026
What Is IT Vendor Management? a Guide for Canadian SMBsLearn what is IT vendor management, its lifecycle, benefits, and risks. Our guide for Canadian SMBs covers best practices for security and compliance.
Read Full Post
June 7, 2026
Legacy System Modernization for Canadian SMBsUnlock growth with legacy system modernization. Our guide helps Canadian SMBs navigate strategies, costs, and risks for a smooth transition to modern IT.
Read Full Post
June 6, 2026
HIPAA Compliance Checklist: A 10-Point Guide for SMBsNavigate HIPAA with our comprehensive HIPAA compliance checklist for Canadian SMBs. Learn 10 actionable steps for safeguarding PHI and avoiding costly fines.
Read Full Post