
May 14, 2026
Office 365 Advantages and Disadvantages: A 2026 GuideExplore the key office 365 advantages and disadvantages for Canadian SMBs. Our guide covers cost, security, collaboration, and how to make the right choice.
Read Full Post%20(1).webp)
Usman Malik
Chief Executive Officer
May 15, 2026
A security alert lands in your inbox at 6:12 a.m. Your office is just opening. Staff need access to email, files, accounting systems, and line-of-business apps. You don't yet know whether the alert is noise, a real attack, or the start of a bad day that turns into a privacy incident.
That's where the ips vs ids decision gets practical fast.
Most Canadian SMBs don't need more acronyms. You need a clear answer to a business question: do you want a system that watches and warns, or one that can step in and stop traffic automatically? The right answer affects risk, uptime, compliance, and how much work lands on your internal IT team.
If you're already reviewing broader leadership priorities, the TekRecruiter cyber security guide for CTOs is a useful companion read because it frames security as an operating issue, not just a technical one.
An intrusion detection system and an intrusion prevention system solve the same core problem from different angles. Both inspect activity for signs of malicious behaviour. They part ways on what happens next.
IDS tells you something looks wrong. IPS tries to stop it.
For many mid-sized businesses, that sounds simple until you map it to reality. A detection-only approach gives you visibility with less chance of disrupting normal operations. A prevention-first approach gives you speed, but if it's tuned poorly, it can interrupt legitimate traffic and create its own business problem.
If your team relies on cloud apps, remote access, shared files, and mobile devices, your network carries far more than basic web traffic. It carries client records, payroll data, patient information, legal documents, and operational workflows. One weak point can trigger a compliance headache and a service interruption at the same time.
That's also why network controls can't sit alone. They need to fit with adjacent layers such as managed firewall services, endpoint protection, and response processes.
Bottom line: In the ips vs ids debate, the right choice depends less on the tool itself and more on your tolerance for delay, disruption, and manual follow-up.
Too many businesses buy based on feature lists. That's a mistake.
Use this lens instead:
The simplest way to understand ips vs ids is this. IDS is the watchdog. IPS is the bodyguard.
The watchdog sees suspicious movement and raises the alarm. The bodyguard stands in the doorway and can stop someone from getting through.
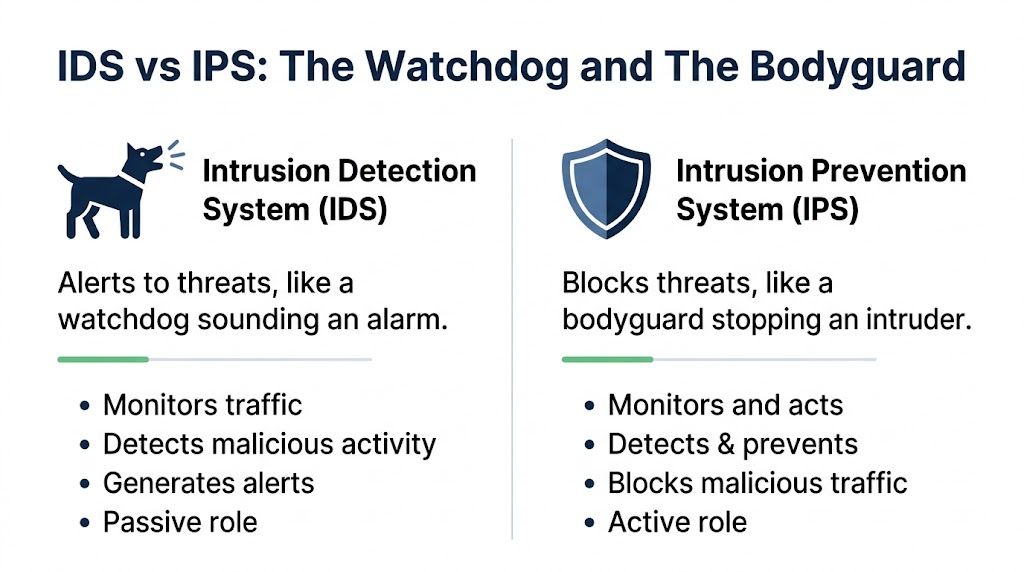
A foundational distinction is architectural. IDS began as a monitoring-and-alerting control, while IPS evolved later to add inline blocking. In practice, IDS is typically deployed out-of-band using a TAP or SPAN port to inspect a copy of traffic, while IPS is deployed inline so it can drop packets, reset connections, or block sessions before they reach a target, as outlined in Fidelis Security's explanation of IDS vs IPS.
That placement decision drives everything else.
| Attribute | Intrusion Detection System (IDS) | Intrusion Prevention System (IPS) |
|---|---|---|
| Primary role | Observe and alert | Detect and block |
| Placement | Out-of-band | Inline |
| Effect on traffic flow | Doesn't sit directly in the traffic path | Sits directly in the traffic path |
| Response style | Requires human follow-up | Can act automatically |
| Best fit | Visibility, investigation, careful tuning | Fast containment, policy enforcement |
An IDS can see bad traffic without touching production flow. That makes it safer to introduce in sensitive environments. If you're worried about accidental disruption, IDS is usually the lower-risk starting point.
An IPS has authority. It can make real-time enforcement decisions before traffic reaches a target. That's powerful, especially when your team can't watch alerts every minute of the day.
A passive control helps you see the problem. An inline control can stop it. That's the trade-off you're buying.
For most mid-sized Canadian businesses, don't treat this as an either-or ideology test. Treat it as a maturity question.
The detection engine is not where IDS and IPS differ most. Both can rely on the same core methods. The fundamental split is what they do after they spot something suspicious.
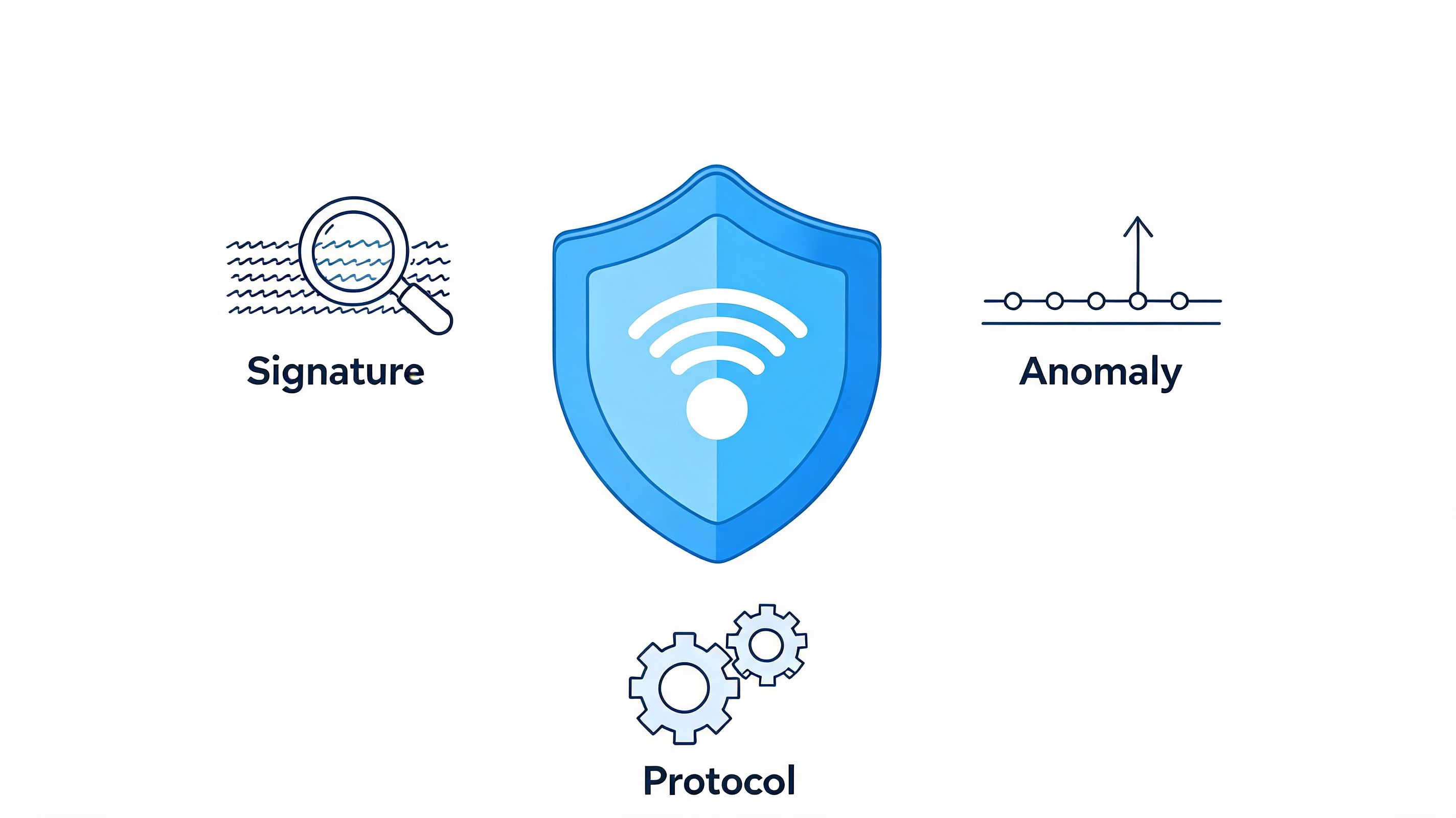
According to Coursera's overview of IDS vs IPS, both IDS and IPS commonly use signature-based detection, statistical anomaly-based detection, and stateful protocol-based detection.
Here's what those mean in business terms:
This is the part that matters operationally. IDS generates alerts that require manual investigation. IPS can automatically apply policies such as dropping packets or resetting connections, based on the same Coursera reference above.
That speed matters. So does the risk.
If a prevention policy is accurate, you contain threats quickly. If it's too aggressive, you can block legitimate business traffic. That's not a technical inconvenience. It can interrupt remote work, customer transactions, access to systems, or communication between business applications.
If your team can't review alerts quickly, an IDS-only model leaves a dangerous gap between detection and action. If your business can't tolerate accidental blocking, an IPS-first model can create avoidable friction.
This is where managed detection and response becomes relevant. It gives you a way to combine better triage with a response process, instead of dumping raw alerts on an already busy internal team.
Practical rule: If your internal staff won't act on alerts consistently, alert-only security won't protect you well enough.
Business owners often ask which tool is “better.” That's the wrong question. Ask which failure is worse for your business.
In healthcare, legal, finance, and manufacturing, both failures can hurt. You need tuning, escalation rules, and ownership. Without that, even a good platform becomes noise.
Where you deploy matters almost as much as what you deploy. The wrong placement leaves blind spots. The right placement aligns security with where your business operates.
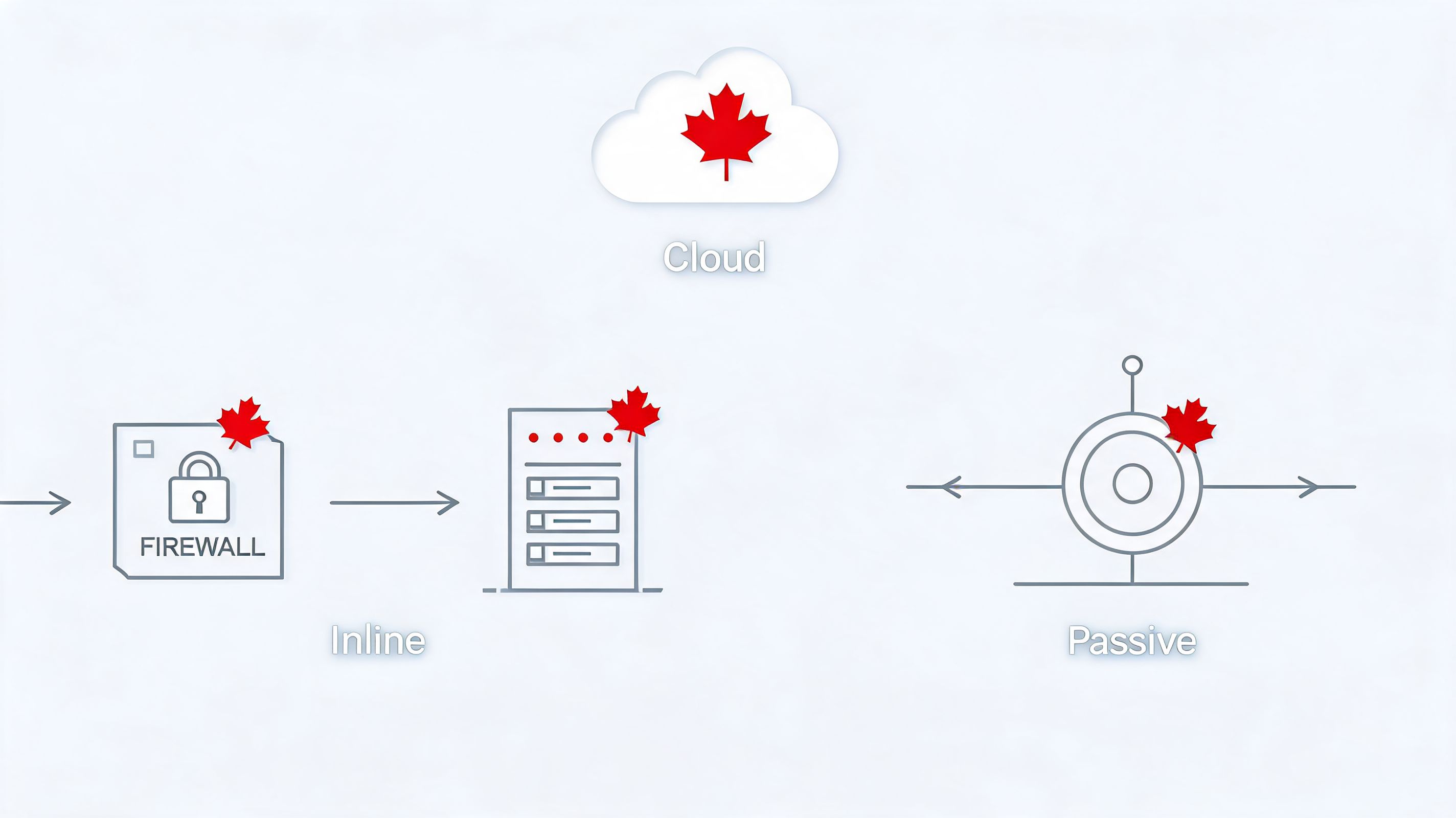
A network-based IDS or IPS watches traffic moving across your environment. This is the classic model. It's useful when you want visibility at the edge, between segments, or near sensitive systems.
This option makes sense if your risk is concentrated around office connectivity, internet-facing services, remote access, or movement between business-critical systems.
A host-based IDS or IPS runs on individual servers or workstations. That helps when the main concern isn't just traffic crossing the network, but what's happening on specific assets.
For example, a file server holding sensitive documents may need deeper visibility into system activity than a perimeter sensor can provide. Host-based controls also help when users, apps, and data don't all sit neatly behind one office firewall anymore.
If your systems are split between on-premises infrastructure and cloud platforms, older placement assumptions break down. You need to think about where your applications live, where your data moves, and how users connect.
That's why the on-prem versus cloud decision isn't separate from security architecture. It's part of it. If your environment spans both, on-cloud vs on-premise planning should sit beside your IDS and IPS design conversation.
Use this order of thinking:
If your business is hybrid, your security controls must be hybrid too. Old diagrams won't save a modern environment.
Generic ips vs ids advice usually ignores the reality of Canadian regulated industries. That's a problem, because architecture choices affect not just security outcomes, but compliance exposure and operational liability.
Healthcare organisations often operate hybrid infrastructure and must align security decisions with PIPEDA and provincial privacy obligations. Existing content often misses this deployment challenge, especially where traditional inline or out-of-band models don't fit hybrid environments, as discussed in TierPoint's analysis of IDS and IPS.
The issue for a clinic is significant. An IPS may help reduce exposure by stopping suspicious activity quickly. But if it's tuned poorly, it could interfere with access to critical systems such as EHR workflows. In healthcare, that's not a minor inconvenience. It can affect patient service and create compliance risk at the same time.
A legal or finance practice often values evidence, traceability, and controlled response. IDS can support that by surfacing suspicious activity for review without automatically interrupting workflows involving client files, trust data, or financial systems.
That said, an alert nobody reviews isn't control. It's theatre. If your internal team is small, prevention at selected choke points may be the more responsible option, especially around internet-facing systems and remote access paths.
For firms handling AI-enabled workflows or sensitive document processing, broader governance also matters. This guide on managing secure enterprise AI data pipelines is worth reading because data handling and detection controls increasingly overlap.
Manufacturers face a different tension. Production continuity matters, but so does segmentation between office systems and operational technology. An aggressive inline policy in the wrong place can interrupt traffic that keeps operations moving. A purely observational approach can leave threats undisturbed too long.
That's why manufacturers should avoid blanket answers. Use detection where visibility and tuning are essential. Use prevention where exposure is high and traffic patterns are stable enough to trust automation.
A broader cyber security services plan matters here because network controls need to connect with endpoint coverage, incident response, and compliance documentation.
In regulated industries, the best control is the one your team can operate safely, prove during review, and trust during an incident.
Most SMBs don't fail because they bought the wrong tool. They fail because nobody owns tuning, triage, escalation, and after-hours response.
That's why I rarely recommend a fully DIY approach for IDS or IPS. These controls need continuous care. Signatures change, normal traffic changes, applications change, and exceptions pile up. If nobody maintains the logic, the system either floods your team with noise or blocks things it shouldn't.
A co-managed model is practical because it splits responsibilities sensibly. External specialists handle monitoring, alert review, and day-to-day security operations. Your internal team keeps business context and decision authority where needed.
That model fits many Canadian mid-market firms. You don't need to build a full internal security operations capability just to get value from these tools.
A workable model usually includes:
If your internal IT team is already stretched, co-managed IT services in Edmonton is a useful reference point for how shared operating models can reduce pressure without giving up control.
The key idea is simple. Detection and prevention tools are only as good as the operating model behind them.
You don't need a perfect answer on day one. You need a defensible one.
The biggest mistake in ips vs ids planning is ignoring the operational cost around the tool. Many comparisons mention false positives but don't quantify the impact for Canadian SMBs. Total expenditure includes investigation overhead from teams chasing false alerts and business disruption from automated blocking. Choosing IPS over IDS requires a break-even analysis against breach risk, and that calculation is specific to your business and risk tolerance, as noted in Corelight's discussion of IDS vs IPS.
| Attribute | Intrusion Detection System (IDS) | Intrusion Prevention System (IPS) |
|---|---|---|
| Core action | Alerts on suspicious activity | Blocks or interrupts suspicious activity |
| Human involvement | Higher | Lower at the moment of enforcement |
| Risk of service disruption | Lower | Higher if poorly tuned |
| Value to investigations | Strong | Useful, but focused on enforcement |
| Best organisational fit | Teams that want visibility and review | Teams that need rapid containment |
Use this rule of thumb:
Your decision shouldn't be based on which acronym sounds stronger. It should be based on which operating risk you're more prepared to manage.
If you want a practical, Canadian-focused assessment of whether IDS, IPS, or a layered co-managed model fits your environment, talk to CloudOrbis Inc.. Their team helps mid-sized organisations align security controls with uptime, compliance, and real-world operational constraints.

May 14, 2026
Office 365 Advantages and Disadvantages: A 2026 GuideExplore the key office 365 advantages and disadvantages for Canadian SMBs. Our guide covers cost, security, collaboration, and how to make the right choice.
Read Full Post
May 13, 2026
Penetration Testing Cost: 2026 SMB Pricing GuideDiscover the penetration testing cost for Canadian SMBs in 2026. Our guide breaks down pricing drivers and budgets for healthcare, finance, and manufacturing.
Read Full Post
May 12, 2026
Microsoft Enterprise License: SMB Guide 2026Navigate Microsoft Enterprise License. Our Canadian SMB guide compares M365 E3/E5, costs, models, & compliance to help you choose the right plan.
Read Full Post